مراقبة
مراقبة Surveillance هي مراقبة السلوك أو الأنشطة أو المعلومات لغرض جمع المعلومات أو التأثير عليها أو إدارتها أو توجيهها.[1][2] يمكن أن يشمل ذلك المراقبة من مسافة بواسطة معدات إلكترونية، مثل الدوائر التلفزيونية (CCTV)، أو اعتراض المعلومات المرسلة إلكترونياً، مثل حركة الإنترنت. يمكن أن تتضمن أيضاً طرقاً تقنية بسيطة، مثل جمع المعلومات البشرية و الاعتراض البريدي.
تُستخدم المراقبة من قبل الحكومات لجمع المعلومات الاستخباراتية، أو منع الجريمة، أو حماية عملية، أو شخص، أو مجموعة أو شيء، أو التحقيق في الجريمة. كما يتم استخدامه من قبل المنظمات الإجرامية للتخطيط لارتكاب الجرائم، ومن قبل الشركات لجمع المعلومات الاستخبارية عن المجرمين أو منافسيهم أو الموردين أو العملاء. قد تقوم المنظمات الدينية المكلفة بالكشف عن هرطقة و عدم الاستقامة بالمراقبة.[3]حيث يقوم المدققون بشكل ما من أشكال المراقبة.[4]
يمكن للحكومات استخدام المراقبة لانتهاك خصوصية الأشخاص بشكل غير مبرر وغالباً ما يتم انتقادها من قبل نشطاء الحريات المدنية.[5]قد يكون لدى الديمقراطيات الليبرالية قوانين تسعى إلى تقييد الاستخدام الحكومي والخاص للمراقبة، بينما نادراً ما يكون لدى الحكومات السلطوية أي قيود محلية. ويبدو أن التجسس الدولي شائع بين جميع أنواع البلدان.[6][7]
أساليب المراقبة
الحاسب
تتضمن الغالبية العظمى من المراقبة الحاسوبية مراقبة البيانات و حركة الإنترنت.[8]في الولايات المتحدة على سبيل المثال، بموجب Communications Assistance For Law Enforcement Act، يجب أن تكون جميع المكالمات الهاتفية وحركة الإنترنت ذات النطاق العريض (رسائل البريد الإلكتروني، وحركة الوب، والرسائل الفورية، وما إلى ذلك) متاحة للمراقبة في الوقت الفعلي دون عوائق من قبل وكالات تنفيذ القانون الفيدرالية.[9][10][11]
يحوي الإنترنت الكثير من البيانات وبسبب عدم قدرة المحققون\المدققون البشريون من البحث فيها يدوياً، تقوم أجهزة الحاسب الآلية للمراقبة عبر الإنترنت بفحص الكم الهائل من حركة الإنترنت التي يتم اعتراضها لتحديد وإبلاغ المحققين البشريين عن الحركة التي تعتبر مثيرة للاهتمام أو مشبوهة. يتم تنظيم هذه العملية من خلال استهداف كلمات أو عبارات "محفزة" معينة، أو زيارة أنواع معينة من مواقع الوب، أو التواصل عبر البريد الإلكتروني أو الدردشة عبر الإنترنت مع أفراد أو مجموعات مشبوهة.[12] تنفق الوكالات مليارات الدولارات سنوياً، مثل وكالة الأمن القومي و مكتب التحقيقات الفدرالي و مكتب التوعية الإعلامية، لتطوير وشراء وتنفيذ وتشغيل أنظمة مثل كارنيڤور و ناروس إنسايت و إتشلون لاعتراض كل هذه البيانات وتحليلها لاستخراج المعلومات المفيدة فقط لأجهزة\وكالات تنفيذ القانون والاستخبارات.[13]
يمكن أن تكون أجهزة الحاسب هدفاً للمراقبة بسبب البيانات الشخصية المخزنة عليها. إذا كان شخص ما قادراً على تثبيت برنامج، مثل مادجك لانترن الخاص بـ FBI و CIPAV، على نظام الحاسب، فيمكنه بسهولة الوصول غير المصرح به إلى هذه البيانات. يمكن تثبيت مثل هذه البرامج مادياً أو عن بُعد.[14]هناك شكل آخر من أشكال المراقبة الحاسوبية، يُعرف باسم van Eck phreaking، يتضمن قراءة الانبعاث الكهرومغناطيسي من الأجهزة الحاسوبية لاستخراج البيانات منها على مسافات تصل إلى مئات الأمتار.[15][16] تدير وكالة الأمن القومي قاعدة بيانات تُعرف باسم "پنويل"، والتي تخزن وتفهرس أعداداً كبيرة من رسائل البريد الإلكتروني لكل من المواطنين الأمريكيين والأجانب.[17][18] بالإضافة إلى ذلك، تدير وكالة الأمن القومي برنامجاً يُعرف باسم پريزم، وهو نظام للتنقيب عن البيانات يمنح حكومة الولايات المتحدة الوصول المباشر إلى المعلومات من شركات التكنولوجيا. من خلال الوصول إلى هذه المعلومات، تستطيع الحكومة الحصول على محفوظات البحث ورسائل البريد الإلكتروني والمعلومات المخزنة والمحادثات الحية ونقل الملفات والمزيد. أثار هذا البرنامج جدلاً كبيراً فيما يتعلق بالمراقبة والخصوصية، خاصة من مواطني الولايات المتحدة.[19][20]
الهواتف
التنصت الرسمي وغير الرسمي على خطوط الهاتف منتشر على نطاق واسع. في الولايات المتحدة على سبيل المثال، يتطلب Communications Assistance For Law Enforcement Act (CALEA أن تكون جميع الاتصالات الهاتفية والمكالمات الصوتية عبر پروتوكول الإنترنت متاحة للتنصت على المكالمات الهاتفية في الوقت الفعلي من قبل سلطات إنفاذ القانون الفيدرالية ووكالات المخابرات.[9][10][11] تمتلك شركتا اتصالات رئيسيتان في الولايات المتحدة - أي تي أند تي و ڤرايزون - عقوداً مع مكتب التحقيقات الفيدرالي، تتطلب منهما الاحتفاظ بسجلات مكالماتهما الهاتفية سهلة البحث والوصول إليها للوكالات الفيدرالية، مقابل 1.8 مليون دولار لكل عام.[21]بين عامي 2003 و 2005، أرسل مكتب التحقيقات الفيدرالي (FBI) أكثر من 140.000 "خطاب الأمن القومي تطلب من شركات الهاتف تسليم معلومات حول مكالمات عملائها وتاريخ الإنترنت. طلب حوالي نصف هذه الرسائل معلومات عن المواطنين الأمريكيين.[22]
لا يلزم وجود وكلاء بشريين لمراقبة معظم المكالمات. ينشئ برنامج تمييز الكلام نصاً يمكن قراءته آلياً من الصوت المعترض، والذي تتم معالجته بعد ذلك بواسطة برامج تحليل المكالمات الآلية، مثل تلك التي طورتها وكالات مثل مكتب التوعية الإعلامية، أو شركات مثل كـ ڤيرنت و ناروس، اللذان يبحثان عن كلمات أو عبارات معينة، لتقرير ما إذا كان سيتم تكريس عامل بشري للمكالمة.[23]
تمتلك أجهزة إنفاذ القانون والاستخبارات في المملكة المتحدة والولايات المتحدة تقنية لتنشيط الميكروفونات في الهواتف المحمولة عن بُعد، من خلال الوصول إلى ميزات التشخيص أو الصيانة الخاصة بالهواتف من أجل الاستماع إلى المحادثات التي تجري بالقرب من الشخص الذي يحمل الهاتف.[24][25][26][27][28][29]
يعد تعقب ستنگراي مثالاً على إحدى هذه الأدوات المستخدمة لمراقبة استخدام الهواتف المحمولة في الولايات المتحدة والمملكة المتحدة. تم تطويرها في الأصل لأغراض مكافحة الإرهاب من قبل الجيش، وهي تعمل عن طريق بث إشارات قوية تجعل الهواتف المحمولة القريبة ترسل رقم IMSI، تماماً كما تفعل مع أبراج الهواتف المحمولة العادية. بمجرد توصيل الهاتف بالجهاز، لا توجد طريقة للمستخدم لمعرفة أنه يتم تعقبه. مشغل ستنگراي قادر على استخراج معلومات مثل الموقع والمكالمات الهاتفية والرسائل النصية، ولكن يُعتقد على نطاق واسع أن قدرات ستنگراي تمتد إلى أبعد من ذلك بكثير. يحيط الكثير من الجدل بشركة ستنگراي بسبب قدراتها القوية والسرية التي تحيط بها.[30]
تستخدم الهواتف المحمولة أيضاً بشكل شائع لجمع بيانات الموقع. يمكن تحديد الموقع الجغرافي للهاتف النقال (وبالتالي الشخص الذي يحمله) بسهولة حتى في حالة عدم استخدام الهاتف، وذلك باستخدام تقنية تُعرف باسم متعدد الأطراف لحساب الاختلافات في الوقت الذي تنتقل فيه الإشارة من الهاتف الخلوي إلى كل من الأبراج الخلوية بالقرب من صاحب الهاتف.[31][32]تم التشكيك في شرعية مثل هذه الأساليب في الولايات المتحدة، ولا سيما ما إذا كان أمر المحكمة مطلوباً.[33]أظهرت سجلات شركة النقل وحدها (Sprint) أنه في سنة معينة طلبت وكالات إنفاذ القانون الفيدرالية بيانات موقع العميل 8 ملايين مرة.[34]

استجابةً لمخاوف خصوصية العملاء في فترة ما بعد إدوارد سنودن،[35]تم تصميم آيفون 6 من أپل لتعطيل جهود التنصت على المكالمات الهاتفية الاستقصائية. يقوم الهاتف بتشفير رسائل البريد الإلكتروني وجهات الاتصال والصور باستخدام رمز تم إنشاؤه بواسطة خوارزمية رياضية معقدة فريدة من نوعها لهاتف فردي ولا يمكن الوصول إليها من قبل أپل.[36] أثارت ميزة التشفير على آيفون 6 انتقادات من مدير مكتب التحقيقات الفيدرالي جيمس ب. أفراد إنفاذ القانون إما لكسر الرمز بأنفسهم أو للحصول على الرمز من مالك الهاتف.[36] نظراً لأن تسريبات سنودن أظهرت أن الوكالات الأمريكية يمكنها الوصول إلى الهواتف في أي مكان في العالم، فقد اشتدت مخاوف الخصوصية في البلدان ذات الأسواق المتنامية للهواتف الذكية، مما يوفر حافزاً قوياً لشركات مثل أپل لمعالجة هذه المخاوف في من أجل تأمين مركزهم في السوق العالمية.[36]
على الرغم من أن CALEA تتطلب من شركات الاتصال عن بعد أن تبني في أنظمتها القدرة على إجراء تنصت قانوني، لم يتم تحديث القانون لمعالجة مشكلة الهواتف الذكية والطلبات للوصول إلى رسائل البريد الإلكتروني و البيانات الوصفية.[37]تُظهر تسريبات سنودن أن وكالة الأمن القومي كانت تستغل هذا الغموض في القانون من خلال جمع البيانات الوصفية حول "مئات الملايين على الأقل" من الأهداف "العرضية" من جميع أنحاء العالم.[37] تستخدم وكالة الأمن القومي أداة تحليلية تُعرف باسم CO-TRAVELER لتتبع الأشخاص الذين تتقاطع حركاتهم وإيجاد أي اتصالات خفية مع الأشخاص محل الاهتمام.[37]
كما كشفت تسريبات سنودن أن المقر الرئيسي للاتصالات الحكومية البريطانية (GCHQ) يمكنهم الوصول إلى المعلومات التي جمعتها وكالة الأمن القومي عن المواطنين الأمريكيين. بمجرد أن يتم جمع البيانات، يمكن لـ GCHQ الاحتفاظ بها لمدة تصل إلى عامين. يمكن تمديد الموعد النهائي بإذن من "مسؤول بريطاني كبير".[38][39]
الكاميرات

كاميرات المراقبة هي كاميرات فيديو تستخدم لغرض مراقبة منطقة ما. غالباً ما تكون متصلة بجهاز تسجيل أو شبكة IP، ويمكن مراقبتها بواسطة حارس الأمن أو مسؤول تنفيذ القانون. كانت الكاميرات ومعدات التسجيل باهظة الثمن نسبياً وتتطلب أفراداً بشريين لمراقبة لقطات الكاميرا، ولكن تحليل اللقطات أصبح أسهل من خلال البرامج الآلية التي تنظم لقطات الفيديو الرقمية في قاعدة بيانات قابلة للبحث، ومن خلال برامج تحليل الفيديو (كـ VIRAT و HumanID). يتم أيضاً تقليل كمية اللقطات بشكل كبير بواسطة مستشعرات الحركة التي تسجل فقط عند اكتشاف الحركة. مع تقنيات الإنتاج الأرخص، تكون كاميرات المراقبة بسيطة وغير مكلفة بما يكفي لاستخدامها في أنظمة الأمن المنزلية والمراقبة اليومية.
اعتباراً من عام 2016، هناك حوالي 350 مليون كاميرا مراقبة في جميع أنحاء العالم. حوالي 65٪ من هذه الكاميرات مثبتة في آسيا. تباطأ نمو الدوائر التلفزيونية في السنوات الأخيرة.[40]في عام 2018، أفادت التقارير أن الصين لديها شبكة مراقبة ضخمة تضم أكثر من 170 مليون كاميرا مراقبة مع 400 مليون كاميرا جديدة من المتوقع أن يتم تركيبها في السنوات الثلاث المقبلة ، وكثير منها يستخدم تقنية التعرف على الأوجه.[41]
في الولايات المتحدة الأمريكية لتركيب أجهزة حديثة للمراقبة بالفيديو. على سبيل المثال، استخدمت مدينة شيكاغو، بولاية إلينوي، مؤخراً موافقة الأمن الداخلي بقيمة 5.1 مليون دولار لتركيب 250 كاميرا مراقبة إضافية، وربطها بمركز مراقبة مركزي، جنباً إلى جنب مع شبكتها الموجودة مسبقاً التي تضم أكثر من 2000 كاميرا، في برنامج يعرف باسم قبة العمليات الافتراضية. في حديثه في عام 2009، أعلن عمدة شيكاغو رتشارد دالي أن شيكاغو سيكون لديها كاميرا مراقبة في كل زاوية شارع بحلول عام 2016.[42][43]تلقت مدينة نيويورك منحة قدرها 350 مليون دولار لتطوير ظام دومين أويرنس،[44] وهو عبارة عن نظام مترابط من أجهزة الاستشعار بما في ذلك 18000 كاميرا CCTV تستخدم للمراقبة المستمرة للمدينة[45]من قبل كل من ضباط الشرطة و أنظمة الذكاء الاصطناعي.[44]
في المملكة المتحدة، لا يتم تشغيل الغالبية العظمى من كاميرات المراقبة بالفيديو من قبل الهيئات الحكومية، ولكن من قبل أفراد أو شركات خاصة، خاصة لمراقبة التصميمات الداخلية للمحلات التجارية والشركات. وفقاً لطلبات قانون حرية المعلومات لعام 2011، كان العدد الإجمالي لكاميرات الدوائر التلفزيونية المغلقة التي تديرها الحكومة المحلية حوالي 52000 في جميع أنحاء المملكة المتحدة.[46] غالباً ما يتم المبالغة في انتشار المراقبة بالفيديو في المملكة المتحدة بسبب التقديرات غير الموثوقة التي يتم إعادة تسعيرها;[47][48]على سبيل المثال تقرير واحد في 2002 استقراء من عينة صغيرة جداً لتقدير عدد الكاميرات في المملكة المتحدة بـ 4.2 مليون (منها 500000 كانت في لندن العظمى).[49]تشير تقديرات أكثر موثوقية إلى أن عدد الكاميرات التي تديرها الحكومة المحلية والخاصة في المملكة المتحدة يبلغ حوالي 1.85 مليون في عام 2011.[50]
في هولندا، أحد الأمثلة على المدن التي توجد بها كاميرات هي لاهاي. هناك، يتم وضع الكاميرات في أحياء المدينة التي يتركز فيها معظم الأنشطة غير القانونية. الأمثلة هي أحياء الأضواء الحمراء ومحطات القطار.[51]
كجزء من مشروع الدرع الذهبي في الصين، تعمل العديد من الشركات الأمريكية، بما في ذلك آيبيإم و جنرال إلكتريك و هنيول، بشكل وثيق مع حكومة الصين لتثبيت ملايين كاميرات المراقبة في جميع أنحاء الصين، جنباً إلى جنب مع تحليل محتوى الفيديو المتقدمة وبرامج التعرف على الوجه، والتي ستحدد وتتعقب الأفراد في كل مكان يذهبون إليه. سيتم توصيلهم بقاعدة بيانات مركزية ومحطة مراقبة، والتي ستحتوي، عند الانتهاء من المشروع، على صورة لوجه كل شخص في الصين: أكثر من 1.3 مليار شخص.[52] ينسب لين جانگ هواي، رئيس مكتب "تكنولوجيا أمن المعلومات" في الصين (المسؤول عن المشروع)، الفضل إلى أنظمة المراقبة في الولايات المتحدة والمملكة المتحدة باعتبارها مصدر إلهام لما يفعله مع مشروع الدرع الذهبي.[52]
تمول وكالة مشروعات الدفاع البحثية المتقدمة (DARPA) مشروعاً بحثياً يسمى Combat Zones That See الذي سيربط الكاميرات عبر المدينة بمحطة مراقبة مركزية، وتحديد الأفراد والمركبات وتتبعهم أثناء تحركهم عبر المدينة، والإبلاغ عن نشاط "مشبوه" (مثل التلويح بالأسلحة، والنظر جنباً إلى جنب، والوقوف في مجموعة، وما إلى ذلك).[53]
في Super Bowl XXXV في يناير 2001، استخدمت الشرطة في تامبا، فلوريدا، برنامج التعرف على الوجه آيدنتكس، فيس آي تي، لفحص الحشد بحثاً عن المجرمين المحتملين والإرهابيين الذين حضروا الحدث[54] (وجدت 19 شخصا لديهم أوامر توقيف معلقة).[55]
[56]غالباً ما تدعي الحكومات في البداية أن الكاميرات مخصصة للاستخدام مراقبة حركة المرور، ولكن ينتهي الأمر بالعديد منها لاستخدامها في المراقبة العامة. على سبيل المثال، كان لدى واشنطن العاصمة 5000 كاميرا "حركة مرور" مثبتة في إطار هذه الفرضية، وبعد أن تم تركيبها جميعاً في مكانها، تم توصيلهم جميعاً معاً ومن ثم منحهم حق الوصول إلى قسم شرطة العاصمة، حتى يتمكنوا من أداء "مرقبة المهام اليومية".[57]
تمت مناقشة تطوير شبكات مركزية لكاميرات الدوائر التلفزيونية التي تراقب المناطق العامة - المرتبطة بقواعد بيانات الحاسب لصور الأشخاص وهويتهم (المقاييس الحيوية)، وقادرة على تتبع تحركات الأشخاص في جميع أنحاء المدينة، وتحديد الأشخاص الذين كانوا معهم - من قبل البعض لتشكيل خطر على الحريات المدنية.[58]وتراپ واير مثال على مثل هذه الشبكة.[59]
تحليل الشبكات الاجتماعية
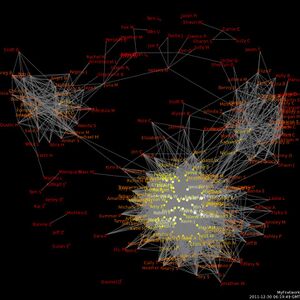
أحد الأشكال الشائعة للمراقبة هو إنشاء خرائط للشبكات الاجتماعية بناءً على البيانات من وسائل التواصل الاجتماعي مثل فيسبوك، مايسپيس، تويتر وكذلك من معلومات تحليل حركة الانترنت من سجلات المكالمات الهاتفية مثل تلك الموجودة في قاعدة بيانات مكالمات وكالة الأمن القومي،[60]وآخرين. يتم بعد ذلك التنقيب في بيانات "خرائط" الشبكات الاجتماعية لاستخراج معلومات مفيدة مثل الاهتمامات الشخصية، والصداقات والانتماءات، والرغبات، والمعتقدات، والأفكار، والأنشطة.[61][62][63]
تستثمر العديد من الوكالات الحكومية الأمريكية، مثل وكالة مشروعات الدفاع البحثية المتقدمة (DARPA) ووكالة الأمن القومي (NSA) ووزارة الأمن الداخلي (DHS) بكثافة في الأبحاث التي تتضمن تحليل الشبكات الاجتماعية.[64][65]يعتقد مجتمع الاستخبارات أن أكبر تهديد لقوة الولايات المتحدة يأتي من الجماعات اللامركزية، بلا قيادة، والمشتتة جغرافياً من الإرهابيين، المخربين، المتطرفين، والمنشقين. تتم مواجهة هذه الأنواع من التهديدات بسهولة من خلال إيجاد العقد المهمة في الشبكة وإزالتها. للقيام بذلك يتطلب خريطة مفصلة للشبكة.[66][67][68]
قال جيسون إثير من جامعة نورث إيسترن، في دراسته لتحليل الشبكات الاجتماعية الحديثة، إن برنامج تحليل الشبكة الاجتماعية القابل للتطوير الذي طوره مكتب التوعية الإعلامية:
الغرض من برنامج خوارزميات SSNA هو توسيع تقنيات تحليل الشبكات الاجتماعية للمساعدة في التمييز بين الخلايا الإرهابية المحتملة والمجموعات الشرعية من الأشخاص .... لكي تكون ناجحاً، سيتطلب SSNA معلومات عن التفاعلات الاجتماعية لغالبية الناس حولها العالم. نظراً لأن وزارة الدفاع لا تستطيع التمييز بسهولة بين المواطنين المسالمين والإرهابيين، فسيكون من الضروري لها جمع البيانات عن المدنيين الأبرياء وكذلك عن الإرهابيين المحتملين.
— جيسون إثير[63]
طورت أي تي أند تي لغة برمجة تسمى "هانكوك"، القادرة على التدقيق في قواعد البيانات الهائلة للمكالمات الهاتفية وسجلات حركة المرور على الإنترنت، مثل قاعدة بيانات مكالمات وكالة الأمن القومي، واستخراج "مجتمعات الاهتمام" —مجموعات الأشخاص الذين يتصلون بعضها البعض بانتظام، أو المجموعات التي تزور بانتظام مواقع معينة على الإنترنت. وقد قامت أي تي أند تي في الأصل ببناء النظام لتطوير "العملاء المحتملين للتسويق"،[69] لكن مكتب التحقيقات الفيدرالي طلب بانتظام مثل هذه المعلومات من شركات الهاتف مثل AT&T دون أمر قضائي،[69] وبعد استخدام البيانات، يخزن جميع المعلومات الواردة في قواعد البيانات الخاصة به، بغض النظر عما إذا كانت المعلومات مفيدة في التحقيق أم لا.[70]
يعتقد بعض الناس أن استخدام مواقع الشبكات الاجتماعية هو شكل من أشكال "المراقبة التشاركية"، حيث يقوم مستخدمو هذه المواقع بشكل أساسي بمراقبة أنفسهم، ووضع معلومات شخصية مفصلة على مواقع الوب العامة حيث يمكن للشركات والحكومات عرضها.[61] في عام 2008، أفاد حوالي 20٪ من أصحاب العمل باستخدام مواقع التواصل الاجتماعي لجمع البيانات الشخصية عن الموظفين المحتملين أو الحاليين.[71]
القياس الحيوي

المراقبة الحيوية هي تقنية تقيس وتحلل الخصائص الجسدية و/أو السلوكية للإنسان لأغراض المصادقة أو تحديد الهوية أو الفحص.[72] تشمل أمثلة الخصائص الجسدية بصمات الأصابع والحمض النووي وأنماط الوجه. تشمل الأمثلة على الخصائص السلوكية في الغالب المشية (طريقة الشخص في المشي) أو الصوت.
التعرف على الوجه هو استخدام التكوين الفريد لملامح وجه الشخص للتعرف عليها بدقة، عادةً من خلال فيديو المراقبة. تمول كل من وزارة الأمن الداخلي وDARPA بشكل كبير الأبحاث في أنظمة التعرف على الوجه.[73]قام مكتب تقنية معالجة المعلومات بتشغيل برنامج يُعرف باسم تحديد الهوية البشرية عن بعد والذي طور تقنيات قادرة على تحديد هوية الشخص حتى بعد 500 ft (150 m) من خلال ملامح وجههم.
شكل آخر من أشكال القياسات الحيوية السلوكية، استناداً إلى الحوسبة العاطفية، يتضمن أجهزة الحاسب التي تتعرف على الحالة العاطفية للشخص بناءً على تحليل تعابير وجهه، ومدى سرعة تحدثه، ونبرة صوته، ووضعه، وغير ذلك الصفات السلوكية. يمكن استخدام هذا على سبيل المثال لمعرفة ما إذا كان سلوك الشخص مشبوهاً (النظر حولك بشكل خفي، أو تعابير الوجه "المتوترة" أو "الغاضبة"، أو التلويح بالأذرع، إلخ.).[74]
التطور الأحدث هو البصمة الوراثية، والذي يبحث في بعض العلامات الرئيسية في الحمض النووي للجسم لإنتاج تطابق. ينفق مكتب التحقيقات الفيدرالي (FBI) مليار دولار لبناء قاعدة بيانات بيومترية جديدة، والتي ستخزن الحمض النووي، وبيانات التعرف على الوجه، وبيانات قزحية العين/شبكية العين، وبصمات الأصابع، وبصمات الكف، وغيرها من البيانات الحيوية للأشخاص الذين يعيشون في الولايات المتحدة. توجد أجهزة الحاسب التي تشغل قاعدة البيانات في منشأة تحت الأرض بحجم ملعبي كرة قدم أمريكي.[75][76][77]
تقوم إدارة شرطة لوس أنجلوس بتثبيت أجهزة التعرف التلقائي على الوجه و التعرف على لوحة الترخيص في سيارات الفرق التابعة لها، وتوفير أجهزة مسح ضوئي للوجه، والتي سيستخدمها الضباط للتعرف على الأشخاص أثناء الدوريات.[78][79][80]
Facial thermographs قيد التطوير، مما يسمح للآلات بتحديد مشاعر معينة لدى الأشخاص مثل الخوف أو التوتر، من خلال قياس درجة الحرارة الناتجة عن تدفق الدم إلى أجزاء مختلفة من الوجه.[81] ويعتقد ضباط إنفاذ القانون أن هذا يمكن أن يحددوا متى يكون المشتبه به عصبياً، مما قد يشير إلى أنهم يخفون شيئاً ما أو يكذبون أو قلقون بشأن شيء ما.[81]
في his paper في الأخلاق وتكنولوجيا المعلومات، يخطط آڤي مارسيانو للأضرار التي تسببها المراقبة الحيوية، ويتتبع نظرياتها ويجمع هذه الأضرار معاً في إطار واحد تكاملي لتوضيح قوتها التراكمية. يقترح مارسيانو أربعة أنواع من الأضرار: الاستخدام غير المصرح به للمعلومات الجسدية ، والحرمان أو الحد من الوصول إلى المساحات المادية، والفرز الاجتماعي الجسدي، وعدم الأهلية الرمزية من خلال بناء التهميش والاختلاف. تنبع القوة الاجتماعية للقياسات الحيوية، وفقاً لمارسيانو، من ثلاث سمات رئيسية: تعقيدها باعتبارها "تقنيات غامضة"، وصورتها العلمية الموضوعية، وفاعليتها المتزايدة، لا سيما في سياق صنع القرار التلقائي.
جوياً
المراقبة الجوية هي تجميع للمراقبة، عادة الصور المرئية أو الفيديو من مركبة محمولة جواً - مثل طائرة بدون طيار، مروحية، أو طائرة تجسس. تستخدم طائرات المراقبة العسكرية مجموعة من أجهزة الاستشعار (مثل الرادار) لمراقبة ساحة المعركة.
ساهمت تكنولوجيا التصوير الرقمي وأجهزة الحاسب المصغرة والعديد من التطورات التكنولوجية الأخرى على مدار العقد الماضي في تحقيق تقدم سريع في أجهزة المراقبة الجوية مثل المركبات الجوية الدقيقة ورؤية أمامية بالأشعة تحت الحمراء والصور عالية الدقة القادرة على تحديد الأشياء على مسافات طويلة للغاية. على سبيل المثال، جنرال أتومكس إمكيو-9 ريپر،[82] طائرة بدون طيار أمريكية مستخدمة للعمليات المحلية من قبل وزارة الأمن الداخلي، وتحمل كاميرات قادرة على تحديد جسم بحجم علبة الحليب من ارتفاعات 30،000 أقدام (9.1 km)، و لديها أجهزة رؤية أمامية بالأشعة تحت الحمراء يمكنها اكتشاف الحرارة من جسم الإنسان على مسافات تصل إلى 60 كيلومتر (37 mi).[83] في حالة سابقة للمراقبة الجوية التجارية، استأجر منتجع التزلج جبل كلنگتون تصويراً جوياً "عيناً في السماء" لمواقف سيارات منافسيه للحكم على نجاح مبادراته التسويقية كما تطورت بدءاً من الخمسينيات.[84]
تقوم وزارة الأمن الداخلي الأمريكية بصدد اختبار الطائرات بدون طيار للقيام بدوريات في سماء الولايات المتحدة لأغراض حماية البنية التحتية الحيوية، ودوريات الحدود، " مراقبة العبور"، والمراقبة العامة لسكان الولايات المتحدة.[85]أجرى قسم شرطة ميامي-ديد اختبارات باستخدام طائرة بدون طيار عمودية للإقلاع والهبوط من هنيول، والتي من المقرر استخدامها في عمليات SWAT.[86]وتختبر إدارة شرطة هيوستن الطائرات بدون طيار ثابتة الجناحين لاستخدامها في "التحكم في حركة المرور".[86]
تعمل المملكة المتحدة أيضاً على خطط لبناء أسطول من الطائرات بدون طيار للمراقبة تتراوح من المركبات الجوية الصغيرة إلى طائرات بدون طيار بحجم كامل، لاستخدامها من قبل قوات الشرطة في جميع أنحاء المملكة المتحدة.[87]
بالإضافة إلى قدرات المراقبة الخاصة بها، فإن مركبة الصعود من المريخ قادرة على حمل مسدس الصعق الكهربائي من أجل "السيطرة على الحشود"، أو أسلحة لقتل المقاتلين الأعداء.[88]
قامت برامج مثل فريق الاستطلاع الجوي غير المتجانس الذي طورته DARPA بأتمتة الكثير من عملية المراقبة الجوية. لقد طوروا أنظمة تتكون من فرق كبيرة لطائرات بدون طيار تقود نفسها، وتقرر تلقائياً من هو "المشبوه" وكيفية متابعة مراقبتها، وتنسيق أنشطتها مع طائرات بدون طيار أخرى قريبة، وإخطار المشغلين البشريين إذا حدث شيء مريب. هذا يزيد بشكل كبير من مساحة المنطقة التي يمكن مراقبتها باستمرار، مع تقليل عدد المشغلين البشريين المطلوبين. وبالتالي، يمكن لسرب من الطائرات الآلية ذاتية التوجيه القيام بدوريات في المدينة تلقائياً وتتبع الأفراد المشتبه بهم، والإبلاغ عن أنشطتهم مرة أخرى إلى محطة مراقبة مركزية.[89][90][91] بالإضافة إلى ذلك، يبحث الباحثون أيضاً في إمكانيات المراقبة الذاتية من قبل مجموعات كبيرة من المركبات الجوية الدقيقة المستقرة بقواعد الحشد اللامركزية المستوحاة من الأحياء.[92][93]
الشركات الكبرى
مراقبة الشركات هي مراقبة سلوك شخص أو مجموعة من قبل شركة. غالباً ما يتم استخدام البيانات التي يتم جمعها لأغراض التسويق أو بيعها لشركات أخرى، ولكن يتم أيضاً مشاركتها بانتظام مع الوكالات الحكومية. يمكن استخدامه كشكل من أشكال ذكاء الأعمال، والذي يمكّن الشركة من تصميم منتجاتها و/أو خدماتها بشكل أفضل لتكون مرغوبة من قبل عملائها. على الرغم من وجود اعتقاد شائع بأن المراقبة يمكن أن تزيد الإنتاجية، إلا أنها قد تؤدي أيضاً إلى عواقب مثل زيادة فرص السلوك المنحرف وخلق عقوبات غير عادلة لأفعالهم. بالإضافة إلى ذلك، يمكن أن تسبب المراقبة مقاومة ورد فعل عنيف لأنها تلمح إلى شك صاحب العمل وانعدام الثقة.[94]
التنقيب في البيانات وتنميطها
التنقيب في البيانات هو تطبيق تقنيات إحصائية وخوارزميات برمجية لاكتشاف العلاقات التي لم يلاحظها أحد من قبل داخل البيانات. تصنيف البيانات في هذا السياق هو عملية تجميع المعلومات حول فرد أو مجموعة معينة من أجل إنشاء ملف تعريف — أي صورة لأنماطهم وسلوكهم. يمكن أن يكون تصنيف البيانات أداة قوية للغاية في تحليل الشبكات الاجتماعية والنفسية. يمكن للمحلل الماهر اكتشاف حقائق عن شخص قد لا يكون واعياً به حتى.[95]
تخلق المعاملات الاقتصادية (مثل مشتريات بطاقات الائتمان) والاجتماعية (مثل المكالمات الهاتفية ورسائل البريد الإلكتروني) في المجتمع الحديث كميات كبيرة من البيانات والسجلات المخزنة. في الماضي، كانت هذه البيانات موثقة في سجلات ورقية، تاركة "أثر ورقي" أو ببساطة لم يتم توثيقها على الإطلاق. كان ربط السجلات الورقية عملية شاقة - فقد تطلبت من مشغلي الاستخبارات البشرية البحث يدوياً في المستندات، الأمر الذي كان يستغرق وقتاً طويلاً وغير مكتمل، في أحسن الأحوال.
لكن العديد من هذه السجلات اليوم إلكترونية، مما أدى إلى " أثر إلكتروني". كل استخدام لجهاز مصرفي، أو الدفع عن طريق بطاقة الائتمان، أو استخدام بطاقة الهاتف، أو الاتصال من المنزل، أو كتاب مكتبة تم فحصه، أو مقطع فيديو مستأجر، أو معاملة مسجلة كاملة، ينتج عنه سجل إلكتروني. يتم بشكل متزايد رقمنة السجلات العامة - مثل سجلات الولادة والمحكمة والضرائب وغيرها - وإتاحتها عبر الإنترنت. بالإضافة إلى ذلك، نظراً لقوانين مثل CALEA، فإن حركة مرور الوب وعمليات الشراء عبر الإنترنت متاحة أيضاً للتنميط. يجعل حفظ السجلات الإلكترونية البيانات قابلة للتجميع والتخزين والوصول بسهولة - بحيث يمكن التجميع والتحليل بكميات كبيرة وفعالة بتكاليف أقل بشكل ملحوظ.
غالباً ما تكون المعلومات المتعلقة بالعديد من هذه المعاملات الفردية متاحة بسهولة لأنها عموماً لا تخضع للحراسة بمعزل عن غيرها، لأن المعلومات، مثل عنوان الفيلم الذي استأجره الشخص، قد لا تبدو حساسة. ومع ذلك، عندما تكون العديد من هذه المعاملات مجمعة يمكن استخدامها لتجميع ملف تعريف مفصل يكشف عن الإجراءات والعادات والمعتقدات والمواقع التي يتردد عليها الاتصالات الاجتماعية وتفضيلات فرد. ثم يتم استخدام ملف التعريف هذا، بواسطة برامج مثل ADVISE[96] و TALON، لتحديد ما إذا كان الشخص يمثل تهديداً عسكرياً أو إجرامياً أو سياسياً.
بالإضافة إلى أدوات التجميع والتنميط الخاصة بها، تستطيع الحكومة الوصول إلى المعلومات من جهات خارجية - على سبيل المثال، البنوك أو شركات الائتمان أو أرباب العمل، وما إلى ذلك - عن طريق طلب الوصول بشكل غير رسمي، عن طريق إجبار الوصول من خلال استخدام مذكرات الاستدعاء أو إجراءات أخرى،[97]أو عن طريق شراء البيانات من مجمعي البيانات التجارية أو وسطاء البيانات. أنفقت الولايات المتحدة 370 مليون دولار على 43 من مراكز الاندماج المخطط لها، وهي شبكة وطنية من مراكز المراقبة الموجودة في أكثر من 30 ولاية. ستقوم المراكز بجمع وتحليل كميات هائلة من البيانات عن المواطنين الأمريكيين. سيحصل على هذه البيانات من خلال دمج المعلومات الشخصية من مصادر مثل وكالات ترخيص القيادة الحكومية، وسجلات المستشفيات، والسجلات الجنائية، والسجلات المدرسية، ومكاتب الائتمان، والبنوك، وما إلى ذلك - ووضع هذه المعلومات في قاعدة بيانات مركزية يمكن الوصول إليها من جميع المراكز، فضلاً عن وكالات إنفاذ القانون والاستخبارات الفيدرالية الأخرى.[98]
بحكم United States v. Miller (1976)، لا تخضع البيانات التي تحتفظ بها جهات خارجية عموماً لمتطلبات التعديل الرابع.
الناشطون البشر
تواجه المنظمات التي لديها أعداء يرغبون في جمع معلومات عن أعضاء الجماعات أو أنشطتها قضايا التسريب.[99]
بالإضافة إلى تسلل العملاء إلى منظمة ما، قد يمارس الطرف المُراقِب ضغطاً على أعضاء معينين في المنظمة المستهدفة للعمل بصفتهم مخبرين (أي للإفصاح عن المعلومات التي بحوزتهم عن المنظمة وأعضائها).[100][101]
يعتبر النشاط الميداني مكلفاً للغاية، وبالنسبة للحكومات التي لديها أدوات مراقبة إلكترونية واسعة النطاق تحت تصرفها، يمكن الحصول على المعلومات التي يتم استردادها من العملاء غالباً من أشكال المراقبة الأقل إشكالية مثل تلك المذكورة أعلاه. ومع ذلك، لا يزال المتسللون البشريون شائعين اليوم. على سبيل المثال، في عام 2007 ظهرت وثائق تظهر أن مكتب التحقيقات الفدرالي كان يخطط لإيفاد ما مجموعه 15000 من العملاء والمخبرين السريين رداً على توجيهات مكافحة الإرهاب التي أرسلها جورج دبليو بوش في عام 2004 والتي أمرت بالاستخبارات وإنفاذ القانون وكالات لزيادة قدراتها HUMINT.[102]
صور السواتل
في 25 مايو 2007، قام مدير المخابرات الوطنية الأمريكية مايكل ماكونيل بتفويض مكتب التطبيقات الوطنية (NAO) التابع لوزارة الأمن الداخلي للسماح للوكالات الفدرالية المحلية والولائية والمحلية بالوصول إلى الصور من سواتل استطلاع المخابرات العسكرية وطائرات الاستطلاع وأجهزة الاستشعار التي يمكن استخدامها الآن لمراقبة أنشطة المواطنين الأمريكيين. ستكون أجهزة استشعار السواتل والطائرات قادرة على اختراق الغطاء السحابي، واكتشاف الآثار الكيميائية، وتحديد الأشياء في المباني و "المخابئ تحت الأرض"، وستوفر فيديو في الوقت الفعلي بدقة أعلى بكثير من الصور الثابتة التي تنتجها برامج مثل جوجل إيرث.[103][104][105][106][107][108]
الهوية وأوراق الاعتماد
أحد أبسط أشكال تحديد الهوية هو حمل أوراق الاعتماد. لدى بعض الدول نظام بطاقة الهوية للمساعدة في تحديد الهوية، بينما تفكر دول أخرى في ذلك ولكنها تواجه معارضة عامة. تُستخدم المستندات الأخرى، مثل جوازات السفر، رخصة قيادة، بطاقة المكتبة، البنوك أو بطاقات الائتمان أيضاً للتحقق من الهوية.
إذا كان شكل بطاقة الهوية "مقروءاً آلياً"، عادةً باستخدام شريط مغناطيسي مشفر أو رقم تعريف (مثل رقم الضمان الاجتماعي)، فإنها تؤكد بيانات تعريف الشخص. في هذه الحالة، قد يُنشئ مساراً إلكترونياً عند فحصه ومسحه ضوئياً، والذي يمكن استخدامه في التنميط، كما هو مذكور أعلاه.
التتبع اللاسلكي
يشير هذا القسم إلى الطرق التي تتضمن مراقبة أجهزة التتبع من خلال مساعدة الإشارات اللاسلكية.
الهواتف المحمولة
تُستخدم الهوائيات الحاملة للجوال أيضاً بشكل شائع لجمع بيانات تحديد الموقع الجغرافي على الهواتف المحمولة. يمكن تحديد الموقع الجغرافي للهاتف المحمول الذي يعمل بالطاقة (وبالتالي الشخص الذي يحمله) بسهولة (سواء تم استخدامه أم لا)، باستخدام تقنية تُعرف باسم متعدد الأطراف لحساب الاختلافات في الزمن لإشارة إلى السفر من الهاتف الخلوي إلى عدة أبراج خلوية بالقرب من مالك الهاتف.[31][32] يشير دكتور ڤيكتور كاپلر[109] من جامعة إيسترن كنتاكي يشير إلى أن مراقبة الشرطة مصدر قلق كبير، مشيراً إلى الإحصائيات التالية من عام 2013:
من بين 321,545 طلباً لإنفاذ القانون تم إرسالها إلى ڤرايزون، كان 54,200 من هذه الطلبات تتعلق بمعلومات "المحتوى" أو "الموقع" - وليس فقط أرقام الهواتف المحمولة أو عناوين IP. تضمنت معلومات المحتوى النص الفعلي للرسائل ورسائل البريد الإلكتروني والتنصت على الصوت أو محتوى الرسائل في الوقت الفعلي.
جهاز المراقبة الجديد نسبياً هو آي إم إس آي كاتشر، وهو جهاز تنصت على الهاتف يستخدم لاعتراض حركة مرور الهاتف المحمول وتتبع حركة مستخدمي الهاتف المحمول. في الأساس يعمل برج المحمول "المزيف" بين الهاتف المحمول المستهدف والأبراج الحقيقية لمزود الخدمة، ويعتبر هجوم رجل في الوسط (MITM). يتم استخدام آي إم إس آي كاتشرز في بعض البلدان من قبل إنفاذ القانون ووكالات الاستخبارات، ولكن استخدامها أثار مخاوف كبيرة تتعلق بالحرية المدنية والخصوصية ويتم تنظيمها بشكل صارم في بعض البلدان.[110]
في مارس 2020، اتهمت صحيفة گارديان اليومية البريطانية، بناءً على مزاعم المبلغين، حكومة المملكة العربية السعودية باستغلال نقاط ضعف شبكة الاتصالات المتنقلة العالمية للتجسس على مواطنيها الذين يسافرون حول الولايات المتحدة.[111] أظهرت البيانات التي شاركها المبلغون عن المخالفات لدعم الادعاءات، أن المملكة كانت تدير حملة تجسس منهجية مستغلة عيوب نظام SS7، وهو نظام مراسلة عالمي. وأظهرت البيانات أن ملايين أوامر التعقب السرية انطلقت من السعودية في مدة أربعة أشهر ابتداء من نوفمبر 2019.[112]
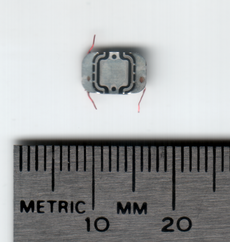
تحديد الهوية بموجات الراديو
تحديد الهوية بموجات الراديو (RFID) هو استخدام أجهزة إلكترونية صغيرة جداً (تسمى "لصاقات RFID") يتم تطبيقها أو دمجها في منتج أو حيوان أو شخص بغرض تحديد الهوية والتتبع باستخدام موجات الراديو . يمكن قراءة العلامات من على بعد عدة أمتار. إنها غير مكلفة للغاية، حيث تكلف بضعة سنتات للقطعة الواحدة، لذلك يمكن إدخالها في العديد من المنتجات اليومية دون زيادة كبيرة في السعر، ويمكن استخدامها لتتبع وتحديد هذه الأشياء لمجموعة متنوعة من الأغراض.
يبدو أن بعض الشركات تقوم "بوضع علامات" على عمالها من خلال دمج علامات RFID في شارات معرف الموظف. نظر العمال في المملكة المتحدة في الإضراب احتجاجاً على وضع علامات على أنفسهم; لقد شعروا أنه نزع الإنسانية أن يتم تعقب جميع تحركاتهم بشرائح RFID.[113][vague] أعرب بعض النقاد عن مخاوفهم من أن يتم تعقب الناس وفحصهم قريباً في كل مكان يذهبون إليه.[114] من ناحية أخرى، أحبطت بطاقات RFID في أساور تعريف الأطفال حديثي الولادة التي وضعتها المستشفيات عمليات اختطاف.[113]
في افتتاحية عام 2003، تكهن كبير المراسلين السياسيين في CNET News.com، ديكلان ماكولا، أنه، قريباً، سيحتوي كل عنصر يتم شراؤه، وربما بطاقات الهوية، على أجهزة RFID، والتي ستستجيب بمعلومات حول الأشخاص أثناء مرورهم. الماسحات الضوئية (ما نوع الهاتف الذي يمتلكونه، ونوع الأحذية التي يرتدونها، والكتب التي يحملونها، وما هي بطاقات الائتمان أو بطاقات العضوية التي يمتلكونها، وما إلى ذلك). يمكن استخدام هذه المعلومات لتحديد الهوية أو التتبع أو التسويق المستهدف. اعتبارا من 2012[تحديث]، لم يحدث هذا إلى حد كبير.[115]
علامات RFID على البشر
غرسة الرقاقة الدقيقة البشرية هي جهاز تحديد الدائرة المتكاملة أو RFID مرسل مستجيب مغطى بزجاج سيليكات ومزروع في جسم الإنسان. عادةً ما تحتوي غرسة تحت الجلد على رقم معرف فريد يمكن ربطه بالمعلومات الواردة في قاعدة بيانات خارجية، مثل التعريف الشخصي والتاريخ الطبي والأدوية والحساسية ومعلومات الاتصال.
طُورت عدة أنواع من الرقائق الدقيقة للتحكم في أنواع معينة من الأشخاص ومراقبتها، مثل المجرمين والشخصيات السياسية والجواسيس، [مطلوب توضيح] سُجلت براءة اختراع رقاقة تتبع "قاتلة" في براءة الاختراع الألمانية ومكتب العلامات التجارية (DPMA) في مايو 2009 تقريباً.
ڤيريتشپ هو جهاز RFID تنتجه شركة تدعى "أپلايد دجيتال سوليوشنز" (ADS). ڤيريتشپ أكبر بقليل من حبة الأرز، ويتم حقنها تحت الجلد. يقال إن الحقنة تشبه تلقي حقنة. الشريحة مغلفة بالزجاج، وتخزن "رقم مشترك VeriChip" الذي يستخدمه الماسح للوصول إلى معلوماتهم الشخصية، عبر الإنترنت، من قاعدة بيانات شركة ڤيريتشپ، "سجل مشترك ڤيريتشپ العالمي". الآلاف من الناس قد أدخلوها بالفعل.[114] في المكسيك، على سبيل المثال، طُلب من 160 عاملاً في مكتب النائب العام حقن الشريحة للتحقق من الهوية والتحكم في الوصول.[116][117]
كما تم استخدام الرقائق الدقيقة القابلة للزرع في أماكن الرعاية الصحية، لكن الباحثين الإثنوغرافيين حددوا عدداً من المشكلات الأخلاقية مع مثل هذه الاستخدامات; وتشمل هذه المشاكل العلاج غير المتكافئ، وتراجع الثقة، واحتمال تعريض المرضى للخطر.[118]
أجهزة تحديد الموقع الجغرافي
نظام تحديد المواقع العالمي
في الولايات المتحدة، قامت الشرطة بزرع أجهزة تتبع GPS في سيارات الأشخاص لمراقبة تحركاتهم،[119]بدون أمر قضائي.[120] في أوائل عام 2009، تم الجدل في المحكمة بأن لديهم الحق في القيام بذلك.[121]
تدير العديد من المدن مشاريع تجريبية لتطلب من المفرج عنهم ارتداء أجهزة GPS لتتبع تحركاتهم عند خروجهم من السجن.[122]
الأجهزة
أجهزة التنصت السري وأجهزة الفيديو، أو "التنصت"، هي أجهزة إلكترونية مخفية تُستخدم لالتقاط وتسجيل و/أو نقل البيانات إلى طرف متلقي مثل وكالة إنفاذ القانون.
أدارت الولايات المتحدة العديد من عمليات الاستخبارات المحلية، مثل COINTELPRO، والتي قامت بالتنصت على منازل ومكاتب ومركبات الآلاف من المواطنين الأمريكيين، عادةً النشطاء السياسيين، المخربين، والمجرمين.[123]
تمتلك أجهزة إنفاذ القانون والاستخبارات في المملكة المتحدة والولايات المتحدة تقنية لتنشيط الميكروفونات في الهواتف المحمولة عن بُعد من خلال الوصول إلى ميزات التشخيص/الصيانة الخاصة بالهاتف، من أجل الاستماع إلى المحادثات التي تجري بالقرب من الشخص الذي يحمل الهاتف.[25][26][27]
الخدمات البريدية
مع تزايد عدد الأشخاص الذين يستخدمون الفاكسات والبريد الإلكتروني، تتضاءل أهمية مراقبة النظام البريدي، لصالح مراقبة الإنترنت والهاتف. لكن اعتراض البريد لا يزال خياراً متاحاً لوكالات إنفاذ القانون والاستخبارات، في ظروف معينة.[124]هذه ليست ممارسة شائعة، ومع ذلك، تتطلب كيانات مثل الجيش الأمريكي مستويات عالية من الموافقة للقيام بذلك.[125]
نفذت الولايات المتحدة وكالة المخابرات المركزية ومكتب التحقيقات الفدرالي اثنتي عشرة حملة منفصلة لفتح البريد تستهدف مواطني الولايات المتحدة. في أحد هذه البرامج، تم اعتراض أكثر من 215000 اتصال وفتحها وتصويرها.[126][127]
المراقبة السرية
المراقبة السرية هي المراقبة المنسقة للموقع أو الشخص. تتم عمليات المراقبة السرية عموماً سراً ولغرض جمع أدلة متعلق بنشاط إجرامي. المصطلح مشتق من ممارسة مساح الأراضي لاستخدام حصص المسح لقياس مساحة قبل بدء مشروع المبنى الرئيسي.
إنترنت الأشياء
إن إنترنت الأشياء (IoT) هو مصطلح يشير إلى مستقبل التكنولوجيا حيث يمكن جمع البيانات دون تفاعل الإنسان والحاسوب. يمكن استخدام إنترنت الأشياء لتحديد الهوية والمراقبة وتتبع الموقع وتتبع الصحة.[128] بينما يتمتع إنترنت الأشياء بميزة كونها أداة لتوفير الوقت تجعل الأنشطة أكثر بساطة، فإنها تثير مخاوف المراقبة الحكومية والخصوصية فيما يتعلق بكيفية استخدام البيانات.[128]
جدل
الدعم
يعتقد مؤيدو أنظمة المراقبة أن هذه الأدوات يمكن أن تساعد في حماية المجتمع من الإرهابيين والمجرمين. وحدث الجدل بشأن المراقبة التي يمكن أن تقلل الجريمة بثلاث وسائل: عن طريق الردع والمراقبة وإعادة الإعمار. يمكن للمراقبة أن تردع عن طريق زيادة فرصة القبض عليهم، ومن خلال الكشف عن طريقة العمل. هذا يتطلب حد أدنى من التوغل.[129]
هناك طريقة أخرى حول كيفية استخدام المراقبة لمحاربة النشاط الإجرامي وهي ربط تدفق المعلومات الذي يتم الحصول عليه منهم بنظام التعرف (على سبيل المثال، نظام الكاميرا الذي يتم تغذيته من خلال نظام التعرف على الوجه). يمكن لهذا على سبيل المثال التعرف التلقائي على الهاربين وتوجيه الشرطة إلى مواقعهم.
يجب التمييز هنا مع ذلك على نوع المراقبة المستخدمة. بعض الأشخاص الذين يقولون إنهم يدعمون المراقبة بالفيديو في شوارع المدينة قد لا يدعمون الصنابير الهاتفية العشوائية والعكس صحيح. إلى جانب الأنواع، فإن الطريقة في كيفية إجراء هذه المراقبة مهمة أيضاً; أي أن النقرات الهاتفية العشوائية يتم دعمها من قبل عدد أقل بكثير من النقرات الهاتفية التي يتم إجراؤها فقط للأشخاص المشتبه في قيامهم بأنشطة غير قانونية.
يمكن أيضاً استخدام المراقبة لمنح العاملين البشريين ميزة تكتيكية من خلال تحسين الوعي بالموقف، أو من خلال استخدام العمليات الآلية، أي تحليل محتوى الفيديو. يمكن أن تساعد المراقبة في إعادة بناء الحادث وإثبات الذنب من خلال توفر لقطات لخبراء الطب الشرعي. يمكن أن تؤثر المراقبة أيضاً على الأمن الشخصي إذا كانت موارد المراقبة مرئية أو إذا كان من الممكن الشعور بعواقب المراقبة.
يمكن أن يكون لبعض أنظمة المراقبة (مثل نظام الكاميرا الذي يتم تشغيل خلاصته من خلال نظام التعرف على الوجه المذكور أعلاه) استخدامات أخرى إلى جانب مكافحة النشاط الإجرامي. على سبيل المثال، يمكن أن تساعد في استعادة الأطفال الهاربين، والبالغين المختطفين أو المفقودين، والأشخاص المعاقين عقلياً. يعتقد المؤيدون الآخرون ببساطة أنه لا يوجد شيء يمكن القيام به حيال فقدان الخصوصية، وأن الناس يجب أن يعتادوا على عدم التمتع بالخصوصية. كما قال الرئيس التنفيذي لشركة صن ميكروسيستيمز سكوت مكنيلي: "ليس لديك أي خصوصية على أي حال. تجاوز ذلك."[130][131]
حجة أخرى شائعة هي: "إذا كنت لا تفعل شيئاً خاطئاً، فلا داعي للخوف. ويترتب على ذلك أنه إذا كان المرء يمارس أنشطة غير قانونية، ففي هذه الحالة لا يكون لديه مبرر شرعي لخصوصيته. ومع ذلك، إذا كانوا يتبعون القانون، فلن تؤثر عليهم المراقبة.[132]
المعارضة
With the advent of programs such as the Total Information Awareness program and ADVISE, technologies such as high speed surveillance computers and biometrics software, and laws such as the Communications Assistance for Law Enforcement Act, governments now possess an unprecedented ability to monitor the activities of their subjects.[133] Many civil rights and privacy groups, such as the Electronic Frontier Foundation and American Civil Liberties Union, have expressed concern that by allowing continual increases in government surveillance of citizens we will end up in a mass surveillance society, with extremely limited, or non-existent political and/or personal freedoms. Fears such as this have led to numerous lawsuits such as Hepting v. AT&T.[133][134]
Some critics state that the claim made by supporters should be modified to read: "As long as we do what we're told, we have nothing to fear.". For instance, a person who is part of a political group which opposes the policies of the national government, might not want the government to know their names and what they have been reading, so that the government cannot easily subvert their organization, arrest, or kill them. Other critics state that while a person might not have anything to hide right now, the government might later implement policies that they do wish to oppose, and that opposition might then be impossible due to mass surveillance enabling the government to identify and remove political threats. Further, other critics point to the fact that most people do have things to hide. For example, if a person is looking for a new job, they might not want their current employer to know this. Also if an employer wishes total privacy to watch over their own employee and secure their financial information it may become impossible, and they may not wish to hire those under surveillance.
In December 2017, the Government of China took steps to oppose widespread surveillance by security-company cameras, webcams, and IP Cameras after tens-of-thousands were made accessible for internet viewing by IT company Qihoo[135]
Totalitarianism
Programs such as the Total Information Awareness program, and laws such as the Communications Assistance For Law Enforcement Act have led many groups to fear that society is moving towards a state of mass surveillance with severely limited personal, social, political freedoms, where dissenting individuals or groups will be strategically removed in COINTELPRO-like purges.[133][134]
Kate Martin, of the Center For National Security Studies said of the use of military spy satellites being used to monitor the activities of U.S. citizens: "They are laying the bricks one at a time for a police state."[107]
Some point to the blurring of lines between public and private places, and the privatization of places traditionally seen as public (such as shopping malls and industrial parks) as illustrating the increasing legality of collecting personal information.[136] Traveling through many public places such as government offices is hardly optional for most people, yet consumers have little choice but to submit to companies' surveillance practices.[137] Surveillance techniques are not created equal; among the many biometric identification technologies, for instance, face recognition requires the least cooperation. Unlike automatic fingerprint reading, which requires an individual to press a finger against a machine, this technique is subtle and requires little to no consent.[137]
Psychological/social effects
Some critics, such as Michel Foucault, believe that in addition to its obvious function of identifying and capturing individuals who are committing undesirable acts, surveillance also functions to create in everyone a feeling of always being watched, so that they become self-policing. This allows the State to control the populace without having to resort to physical force, which is expensive and otherwise problematic.[138]
With the development of digital technology, individuals have become increasingly perceptible to one another, as surveillance becomes virtual. Online surveillance is the utilization of the internet to observe one's activity.[139] Corporations, citizens, and governments participate in tracking others' behaviours for motivations that arise out of business relations, to curiosity, to legality. In her book Superconnected, Mary Chayko differentiates between two types of surveillance: vertical and horizontal.[139] Vertical surveillance occurs when there is a dominant force, such as the government that is attempting to control or regulate the actions of a given society. Such powerful authorities often justify their incursions as a means to protect society from threats of violence or terrorism. Some individuals question when this becomes an infringement on civil rights.[139]
Horizontal diverges from vertical surveillance as the tracking shifts from an authoritative source to an everyday figure, such as a friend, coworker, or stranger that is interested in one's mundane activities.[139] Individuals leave traces of information when they are online that reveal their interests and desires of which others observe. While this can allow people to become interconnected and develop social connections online, it can also increase potential risk to harm, such as cyberbullying or censoring/stalking by strangers, reducing privacy.[139]
In addition, Simone Browne argues that surveillance wields an immense racializing quality such that it operates as "racializing surveillance." Browne uses racializing surveillance to refer to moments when enactments of surveillance are used to reify boundaries, borders, and bodies along racial lines and where the outcome is discriminatory treatment of those who are negatively racialized by such surveillance. Browne argues racializing surveillance pertains to policing what is "in or out of place."[140][141]
Privacy
Numerous civil rights groups and privacy groups oppose surveillance as a violation of people's right to privacy. Such groups include: Electronic Privacy Information Center, Electronic Frontier Foundation, American Civil Liberties Union and Privacy International.
There have been several lawsuits such as Hepting v. AT&T and EPIC v. Department of Justice by groups or individuals, opposing certain surveillance activities.
Legislative proceedings such as those that took place during the Church Committee, which investigated domestic intelligence programs such as COINTELPRO, have also weighed the pros and cons of surveillance.
- Court Cases
People vs. Diaz (2011) was a court case in the realm of cell phone privacy, even though the decision was later overturned. In this case, Gregory Diaz was arrested during a sting operation for attempting to sell ecstasy. During his arrest, police searched Diaz's phone and found more incriminating evidence including SMS text messages and photographs depicting illicit activities. During his trial, Diaz attempted to have the information from his cell phone removed from evidence, but the courts deemed it as lawful and Diaz's appeal was denied on the California State Court level and, later, the Supreme Court level. Just three short years after, this decision was overturned in the case Riley vs. California (2014).[142]
Riley vs. California (2014) was an Supreme Court case in which a man was arrested for his involvement in a drive-by shooting. A few days after the shooting the police made an arrest of the suspect (Riley), and, during the arrest, the police searched him. However, this search was not only of Riley's person, but also the police opened and searched his cell phone, finding pictures of other weapons, drugs, and of Riley showing gang signs. In court, the question arose whether searching the phone was lawful or if the search was protected by the 4th amendment of the constitution. The decision held that the search of Riley's cell phone during the arrest was illegal, and that it was protected by the 4th Amendment.[143]
Countersurveillance, inverse surveillance, sousveillance
Countersurveillance is the practice of avoiding surveillance or making surveillance difficult. Developments in the late twentieth century have caused counter surveillance to dramatically grow in both scope and complexity, such as the Internet, increasing prevalence of electronic security systems, high-altitude (and possibly armed) UAVs, and large corporate and government computer databases.[144]
Inverse surveillance is the practice of the reversal of surveillance on other individuals or groups (e.g., citizens photographing police). Well-known examples include George Holliday's recording of the Rodney King beating and the organization Copwatch, which attempts to monitor police officers to prevent police brutality. Counter-surveillance can be also used in applications to prevent corporate spying, or to track other criminals by certain criminal entities. It can also be used to deter stalking methods used by various entities and organizations.
Sousveillance is inverse surveillance, involving the recording by private individuals, rather than government or corporate entities.[145]
Popular culture
In literature
- George Orwell's novel Nineteen Eighty-Four portrays a fictional totalitarian surveillance society with a very simple mass surveillance system consisting of human operatives, informants, and two-way "telescreens" in people's homes. Because of the impact of this book, mass-surveillance technologies are commonly called "Orwellian" when they are considered problematic.
- The novel mistrust highlights the negative effects from the overuse of surveillance at Reflection House. The central character Kerryn installs secret cameras to monitor her housemates – see also Paranoia.
- The book The Handmaid's Tale, as well as a film and TV series based on it, portray a totalitarian Christian theocracy where all citizens are kept under constant surveillance.
- In the book The Girl with the Dragon Tattoo, Lisbeth Salander uses computers to get information on people, as well as other common surveillance methods, as a freelancer.
- V for Vendetta, a British graphic novel written by Alan Moore
- David Egger's novel The Circle exhibits a world where a single company called "The Circle" produces all of the latest and highest quality technologies from computers and smartphones, to surveillance cameras known as "See-Change cameras". This company becomes associated with politics when starting a movement where politicians go "transparent" by wearing See-Change cameras on their body to prevent keeping secrets from the public about their daily work activity. In this society, it becomes mandatory to share personal information and experiences because it is The Circle's belief that everyone should have access to all information freely. However, as Eggers illustrates, this takes a toll on the individuals and creates a disruption of power between the governments and the private company. The Circle presents extreme ideologies surrounding mandatory surveillance. Eamon Bailey, one of the Wise Men, or founders of The Circle, believes that possessing the tools to access information about anything or anyone, should be a human right given to all of the world's citizens.[146] By eliminating all secrets, any behaviour that has been deemed shameful will either become normalized or no longer considered shocking. Negative actions will eventually be eradicated from society altogether, through the fear of being exposed to other citizens[146] This would be achieved in part by everyone going transparent, something that Bailey highly supports, although it's notable that none of the Wise Men ever became transparent themselves. One major goal of The Circle is to have all of the world's information filtered through The Circle, a process they call "Completion".[146] A single, private company would then have full access and control over all information and privacy of individuals and governments. Ty Gospodinov, the first founder of The Circle, has major concerns about the completion of the circle. He warns that this step would give The Circle too much power and control, and would quickly lead to totalitarianism.
In music
- The Dead Kennedys' song "I Am The Owl" is about government surveillance and social engineering of political groups.
- The Vienna Teng song "Hymn of Acxiom" is about corporate data collection and surveillance.
Onscreen
- The film Gattaca portrays a society that uses biometric surveillance to distinguish between people who are genetically engineered "superior" humans and genetically natural "inferior" humans.
- In the movie Minority Report, the police and government intelligence agencies use micro aerial vehicles in SWAT operations and for surveillance purposes.
- HBO's crime-drama series The Sopranos regularly portrays the FBI's surveillance of the DiMeo Crime Family. Audio devices they use include "bugs" placed in strategic locations (e.g., in "I Dream of Jeannie Cusamano" and "Mr. Ruggerio's Neighborhood") and hidden microphones worn by operatives (e.g., in "Rat Pack") and informants (e.g., in "Funhouse", "Proshai, Livushka" and "Members Only"). Visual devices include hidden still cameras (e.g., in "Pax Soprana") and video cameras (e.g., in "Long Term Parking").
- The movie THX-1138 portrays a society wherein people are drugged with sedatives and antidepressants, and have surveillance cameras watching them everywhere they go.
- The movie The Lives of Others portrays the monitoring of East Berlin by agents of the Stasi, the GDR's secret police.
- The movie The Conversation portrays many methods of audio surveillance.
- The movie V for Vendetta, a 2005 dystopian political thriller film directed by James McTeigue and written by the Wachowskis, is about British government trying to brainwash people by media, obtain their support by fearmongering, monitor them by mass surveillance devices, and suppress or kill any political or social objection.
- The movie Enemy of the State a 1998 American action-thriller film directed by Tony Scott is about using U.S. citizens' data to search their background and surveillance devices to capture everyone that is identified as "enemy".
- The British TV series The Capture explores the potential for video surveillance to be manipulated in order to support a conviction to pursue a political agenda.
See also
- Mass surveillance in the United States
- Sousveillance
- Surveillance art
- Surveillance capitalism
- Surveillance system monitor
- Trapwire
- Participatory surveillance
References
- ^ Lyon, David (2001). Surveillance Society: Monitoring in Everyday Life. Philadelphia: Open University Press. ISBN 978-0-335-20546-2.
- ^ Monahan, Torin; Murakami Wood, David (2018). Surveillance Studies: A Reader. New York: Oxford University Press. ISBN 9780190297824.
- ^
Greenleaf, Richard E. (2018). "Historiography of the Mexican Inquisition: Evolution of Interpretations and Methodologies". In Perry, Mary Elizabeth; Cruz, Anne J. (eds.). Cultural Encounters: The Impact of the Inquisition in Spain and the New World. Center for Medieval and Renaissance Studies, UCLA. Vol. 24. Berleley: University of California Press. p. 260. ISBN 9780520301245. Retrieved مارس 14, 2020.
Studies [...] are based partially on Inquisition surveillance of foreigners and Protestants.
- ^
Cardwell, Harvey (2005). Principles of Audit Surveillance. R.T. Edwards, Inc. p. 102. ISBN 9781930217133. Retrieved مارس 14, 2020.
[...] accounts and inventories alike are generally within the area of surveillance of the auditor [...].
- ^ Stallman, Richard M. (أكتوبر 14, 2013). "Stallman: How Much Surveillance Can Democracy Withstand?". Wired. ISSN 1059-1028. Retrieved أبريل 15, 2020.
- ^ "The Psychology of Espionage" (PDF). The Psychology of Espionage.
- ^ "The Unresolved Equation of Espionage and International Law". The Unresolved Equation of Espionage and International Law.
- ^ Diffie, Whitfield; Susan Landau (أغسطس 2008). "Internet Eavesdropping: A Brave New World of Wiretapping". Scientific American. Retrieved مارس 13, 2009.
- ^ أ ب "CALEA Archive – Electronic Frontier Foundation". Electronic Frontier Foundation (website). Archived from the original on مايو 3, 2009. Retrieved مارس 14, 2009.
- ^ أ ب "CALEA: The Perils of Wiretapping the Internet". Electronic Frontier Foundation (website). Retrieved مارس 14, 2009.
- ^ أ ب "CALEA: Frequently Asked Questions". Electronic Frontier Foundation (website). سبتمبر 20, 2007. Retrieved مارس 14, 2009.
- ^ Hill, Michael (أكتوبر 11, 2004). "Government funds chat room surveillance research". USA Today. Associated Press. Retrieved مارس 19, 2009.
- ^ McCullagh, Declan (يناير 30, 2007). "FBI turns to broad new wiretap method". ZDNet News. Retrieved سبتمبر 26, 2014.
- ^ "FBI's Secret Spyware Tracks Down Teen Who Made Bomb Threats". Wired Magazine. يوليو 18, 2007.
- ^ Van Eck, Wim (1985). "Electromagnetic Radiation from Video Display Units: An Eavesdropping Risk?" (PDF). Computers & Security. 4 (4): 269–286. CiteSeerX 10.1.1.35.1695. doi:10.1016/0167-4048(85)90046-X.
- ^ Kuhn, M.G. (2004). "Electromagnetic Eavesdropping Risks of Flat-Panel Displays" (PDF). 4th Workshop on Privacy Enhancing Technologies: 23–25.
- ^ Risen, James; Lichtblau, Eric (يونيو 16, 2009). "E-Mail Surveillance Renews Concerns in Congress". The New York Times. pp. A1. Retrieved يونيو 30, 2009.
- ^ Ambinder, Marc (يونيو 16, 2009). "Pinwale And The New NSA Revelations". The Atlantic. Retrieved يونيو 30, 2009.
- ^ Greenwald; Ewen, Glen; MacAskill (يونيو 6, 2013). "NSA Prism program taps in to user data of Apple, Google and others" (PDF). The Guardian. Retrieved فبراير 1, 2017.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Sottek, T.C.; Kopfstein, Janus (يوليو 17, 2013). "Everything you need to know about PRISM". The Verge. Retrieved فبراير 13, 2017.
- ^ Singel, Ryan (سبتمبر 10, 2007). "Rogue FBI Letters Hint at Phone Companies' Own Data Mining Programs – Updated". Threat Level. Wired. Retrieved مارس 19, 2009.
- ^ Roland, Neil (مارس 20, 2007). "Mueller Orders Audit of 56 FBI Offices for Secret Subpoenas". Bloomberg News. Retrieved مارس 19, 2009.
- ^ Piller, Charles; Eric Lichtblau (يوليو 29, 2002). "FBI Plans to Fight Terror With High-Tech Arsenal". LA Times. Retrieved مارس 14, 2009.
- ^ Schneier, Bruce (ديسمبر 5, 2006). "Remotely Eavesdropping on Cell Phone Microphones". Schneier On Security. Retrieved ديسمبر 13, 2009.
- ^ أ ب McCullagh, Declan; Anne Broache (ديسمبر 1, 2006). "FBI taps cell phone mic as eavesdropping tool". CNet News. Archived from the original on نوفمبر 10, 2013. Retrieved مارس 14, 2009.
- ^ أ ب Odell, Mark (أغسطس 1, 2005). "Use of mobile helped police keep tabs on suspect". Financial Times. Retrieved مارس 14, 2009.
- ^ أ ب "Telephones". Western Regional Security Office (NOAA official site). 2001. Retrieved مارس 22, 2009.
- ^ "Can You Hear Me Now?". ABC News: The Blotter. Archived from the original on أغسطس 25, 2011. Retrieved ديسمبر 13, 2009.
- ^ Coughlin, Kevin (ديسمبر 13, 2006). "Even if they're off, cellphones allow FBI to listen in". The Seattle Times. Retrieved ديسمبر 14, 2009.
- ^ Hampton, Brittany (2012). "From Smartphones to Stingrays: Can the Fourth Amendment Keep up with the Twenty-First Century Note". University of Louisville Law Review. Fifty One: 159–176 – via Law Journal Library.
- ^ أ ب "Tracking a suspect by mobile phone". BBC News. أغسطس 3, 2005. Retrieved مارس 14, 2009.
- ^ أ ب Miller, Joshua (مارس 14, 2009). "Cell Phone Tracking Can Locate Terrorists – But Only Where It's Legal". FOX News. Archived from the original on مارس 18, 2009. Retrieved مارس 14, 2009.
- ^ Samuel, Ian (2008). "Warrantless Location Tracking". N.Y.U. Law Review. SSRN 1092293.
- ^ Zetter, Kim (ديسمبر 1, 2009). "Threat Level Privacy, Crime and Security Online Feds 'Pinged' Sprint GPS Data 8 Million Times Over a Year". Wired Magazine: Threat Level. Retrieved ديسمبر 5, 2009.
- ^ "Greenstone Digital Library Software". snowdenarchive.cjfe.org. Retrieved يونيو 3, 2017.
- ^ أ ب ت Sanger, David (سبتمبر 26, 2014). "Signaling Post-Snowden Era, New iPhone Locks Out N.S.A". The New York Times. Retrieved نوفمبر 1, 2014.
- ^ أ ب ت Gellman, Barton (ديسمبر 4, 2013). "NSA tracking cellphone locations worldwide, Snowden documents show". The Washington Post. Retrieved نوفمبر 1, 2014.
- ^ Ball, James (أكتوبر 29, 2014). "GCHQ views data without a warrant, government admits". The Guardian.
- ^ Szoldra, Paul. "This is everything Edward Snowden revealed in one year of unprecedented top-secret leaks". Business Insider.
- ^ "Rise of Surveillance Camera Installed Base Slows". مايو 5, 2016. Retrieved يناير 5, 2017.
- ^ "Smart cameras catch man in 60,000 crowd". BBC News (in الإنجليزية البريطانية). أبريل 13, 2018. Retrieved أبريل 13, 2018.
- ^ Spielman, Fran (فبراير 19, 2009). "Surveillance cams help fight crime, city says". Chicago Sun Times. Retrieved مارس 13, 2009.[dead link]
- ^ Schorn, Daniel (سبتمبر 6, 2006). "We're Watching: How Chicago Authorities Keep An Eye On The City". CBS News. Retrieved مارس 13, 2009.
- ^ أ ب Levine, E. S.; Tisch, Jessica; Tasso, Anthony; Joy, Michael (فبراير 2017). "The New York City Police Department's Domain Awareness System". Interfaces. 47 (1): 70–84. doi:10.1287/inte.2016.0860.
- ^ Parascandola, Rocco. "New NYPD surveillance cameras to cover stretch of Upper East Side not easily reached by patrol cars". nydailynews.com. Retrieved نوفمبر 1, 2019.
- ^ "The Price of Privacy: How local authorities spent £515m on CCTV in four years" (PDF). Big Brother Watch. فبراير 2012. p. 30. Archived from the original (PDF) on سبتمبر 23, 2015. Retrieved فبراير 4, 2015.
- ^ "FactCheck: how many CCTV cameras?". Channel 4 News. يونيو 18, 2008. Retrieved مايو 8, 2009.
- ^ "You're being watched: there's one CCTV camera for every 32 people in UK – Research shows 1.85m machines across Britain, most of them indoors and privately operated". The Guardian. مارس 2, 2011. Retrieved يناير 7, 2017; "In the press: How the media is reporting the 1.85 million cameras story". Security News Desk. مارس 3, 2011. Retrieved يناير 7, 2017.
- ^ "CCTV in London" (PDF). Retrieved يوليو 22, 2009.
- ^ "How many cameras are there?". CCTV User Group. يونيو 18, 2008. Archived from the original on أكتوبر 23, 2008. Retrieved مايو 8, 2009.
- ^ Den Haag. "Camera surveillance". Archived from the original on أكتوبر 8, 2016. Retrieved ديسمبر 2, 2016.
- ^ أ ب Klein, Naomi (مايو 29, 2008). "China's All-Seeing Eye". Rolling Stone. Archived from the original on مارس 26, 2009. Retrieved مارس 20, 2009.
- ^ "Big Brother To See All, Everywhere". CBS News. Associated Press. يوليو 1, 2003. Retrieved سبتمبر 26, 2014.
- ^ Bonsor, K. (سبتمبر 4, 2001). "How Facial Recognition Systems Work". Retrieved يونيو 18, 2006.
- ^ McNealy, Scott. "Privacy is (Virtually) Dead". Retrieved ديسمبر 24, 2006.
- ^ Roebuck, Kevin (أكتوبر 24, 2012). Communication Privacy Management. ISBN 9781743332900.
- ^ "WIKILEAKS: Surveillance Cameras Around The Country Are Being Used In A Huge Spy Network". Retrieved أكتوبر 5, 2016.
- ^ "EPIC Video Surveillance Information Page". EPIC. Retrieved مارس 13, 2009.
- ^ Hedgecock, Sarah (أغسطس 14, 2012). "TrapWire: The Less-Than-Advertised System To Spy On Americans". The Daily Beast. Retrieved سبتمبر 13, 2012.
- ^ Keefe, Patrick (مارس 12, 2006). "Can Network Theory Thwart Terrorists?". The New York Times.
- ^ أ ب Albrechtslund, Anders (مارس 3, 2008). "Online Social Networking as Participatory Surveillance". First Monday. 13 (3). doi:10.5210/fm.v13i3.2142.
- ^ Fuchs, Christian (2009). Social Networking Sites and the Surveillance Society. A Critical Case Study of the Usage of studiVZ, Facebook, and MySpace by Students in Salzburg in the Context of Electronic Surveillance (PDF). Salzburg and Vienna: Forschungsgruppe Unified Theory of Information. ISBN 978-3-200-01428-2. Retrieved يوليو 28, 2012.
- ^ أ ب Ethier, Jason. "Current Research in Social Network Theory". Northeastern University College of Computer and Information Science. Archived from the original on نوفمبر 16, 2004. Retrieved مارس 15, 2009.
{{cite web}}: CS1 maint: bot: original URL status unknown (link) - ^ Kawamoto, Dawn (يونيو 9, 2006). "Is the NSA reading your MySpace profile?". CNET News. Retrieved مارس 16, 2009.
- ^ Ethier, Jason. "Current Research in Social Network Theory". Northeastern University College of Computer and Information Science. Archived from the original on فبراير 26, 2015. Retrieved مارس 15, 2009.
- ^ Ressler, Steve (يوليو 2006). "Social Network Analysis as an Approach to Combat Terrorism: Past, Present, and Future Research". Homeland Security Affairs. II (2). Retrieved مارس 14, 2009.
- ^ "DyDAn Research Blog". DyDAn Research Blog (official blog of DyDAn). Retrieved ديسمبر 20, 2009.
- ^ أ ب Singel, Ryan (أكتوبر 29, 2007). "AT&T Invents Programming Language for Mass Surveillance". Threat Level. Wired. Retrieved مارس 19, 2009.
- ^ Singel, Ryan (أكتوبر 16, 2007). "Legally Questionable FBI Requests for Calling Circle Info More Widespread than Previously Known". Threat Level. Wired. Retrieved مارس 19, 2009.
- ^ Havenstein, Heather (سبتمبر 12, 2008). "One in five employers uses social networks in hiring process". Computer World. Archived from the original on سبتمبر 23, 2008. Retrieved مارس 14, 2009.
- ^ Woodward, John; Christopher Horn; Julius Gatune; Aryn Thomas (2003). Biometrics: A Look at Facial Recognition. RAND Corporation. ISBN 978-0-8330-3302-4. Retrieved مارس 15, 2009.
- ^ Frank, Thomas (مايو 10, 2007). "Face recognition next in terror fight". USA Today. Retrieved مارس 16, 2009.
- ^ Vlahos, James (يناير 2008). "Surveillance Society: New High-Tech Cameras Are Watching You". Popular Mechanics. Archived from the original on ديسمبر 19, 2007. Retrieved مارس 14, 2009.
- ^ Nakashima, Ellen (ديسمبر 22, 2007). "FBI Prepares Vast Database Of Biometrics: $1 Billion Project to Include Images of Irises and Faces". The Washington Post. pp. A01. Retrieved مايو 6, 2009.
- ^ Arena, Kelly; Carol Cratty (فبراير 4, 2008). "FBI wants palm prints, eye scans, tattoo mapping". CNN. Retrieved مارس 14, 2009.
- ^ Gross, Grant (فبراير 13, 2008). "Lockheed wins $1 billion FBI biometric contract". IDG News Service. InfoWorld. Archived from the original on يونيو 17, 2008. Retrieved مارس 18, 2009.
- ^ "LAPD: We Know That Mug". Wired Magazine. Associated Press. ديسمبر 26, 2004. Retrieved مارس 18, 2009.
- ^ Mack, Kelly. "LAPD Uses Face Recognition Technology To Fight Crime". NBC4 TV (transcript from Officer.com). Archived from the original on مارس 30, 2010. Retrieved ديسمبر 20, 2009.
- ^ Willon, Phil (سبتمبر 17, 2009). "LAPD opens new high-tech crime analysis center". LA Times. Retrieved ديسمبر 20, 2009.
- ^ أ ب Dotinga, Randy (أكتوبر 14, 2004). "Can't Hide Your Lying ... Face?". Wired Magazine. Retrieved مارس 18, 2009.
- ^ Boyd, Ryan. "MQ-9 Reaper" (in الإنجليزية). Retrieved أكتوبر 5, 2016.
- ^ Friedersdorf, Conor (مارس 10, 2016). "The Rapid Rise of Federal Surveillance Drones Over America" (in الإنجليزية الأمريكية). Retrieved أكتوبر 5, 2016.
- ^ Edwards, Bruce, "Killington co-founder Sargent dead at 83" Archived سبتمبر 4, 2015 at the Wayback Machine, Rutland Herald, November 9, 2012. Retrieved December 10, 2012.
- ^ McCullagh, Declan (مارس 29, 2006). "Drone aircraft may prowl U.S. skies". CNet News. Retrieved مارس 14, 2009.
- ^ أ ب Warwick, Graham (يونيو 12, 2007). "US police experiment with Insitu, Honeywell UAVs". FlightGlobal.com. Retrieved مارس 13, 2009.
- ^ La Franchi, Peter (يوليو 17, 2007). "UK Home Office plans national police UAV fleet". Flight International. Retrieved مارس 13, 2009.
- ^ "No Longer Science Fiction: Less Than Lethal & Directed Energy Weapons". International Online Defense Magazine. فبراير 22, 2005. Retrieved مارس 15, 2009.
- ^ "HART Overview" (PDF). IPTO (DARPA) – Official website. أغسطس 2008. Archived from the original (PDF) on ديسمبر 5, 2008. Retrieved مارس 15, 2009.
- ^ "BAA 04-05-PIP: Heterogeneous Airborne Reconnaissance Team (HART)" (PDF). Information Processing Technology Office (DARPA) – Official Website. ديسمبر 5, 2003. Archived from the original (PDF) on نوفمبر 27, 2008. Retrieved مارس 16, 2009.
- ^ Sirak, Michael (نوفمبر 29, 2007). "DARPA, Northrop Grumman Move Into Next Phase of UAV Control Architecture". Defense Daily. Archived from the original on مارس 9, 2012. Retrieved مارس 16, 2009.
- ^ Saska, M.; Chudoba, J.; Preucil, L.; Thomas, J.; Loianno, G.; Tresnak, A.; Vonasek, V.; Kumar, V. Autonomous Deployment of Swarms of Micro-Aerial Vehicles in Cooperative Surveillance. In Proceedings of 2014 International Conference on Unmanned Aircraft Systems (ICUAS). 2014.
- ^ Saska, M.; Vakula, J.; Preucil, L. Swarms of Micro Aerial Vehicles Stabilized Under a Visual Relative Localization. In ICRA2014: Proceedings of 2014 IEEE International Conference on Robotics and Automation. 2014.
- ^ Anthony, Denise (2017). "Toward a Sociology of Privacy". Annual Review of Sociology. 43 (1): 249–269. doi:10.1146/annurev-soc-060116-053643.
- ^ Hildebrandt, Mireille; Serge Gutwirth (2008). Profiling the European Citizen: Cross Disciplinary Perspectives. Dordrecht: Springer. ISBN 978-1-4020-6913-0.
- ^ Clayton, Mark (فبراير 9, 2006). "US Plans Massive Data Sweep". Christian Science Monitor. Retrieved مارس 13, 2009.
- ^ Flint, Lara (سبتمبر 24, 2003). "Administrative Subpoenas for the FBI: A Grab for Unchecked Executive Power". The Center For Democracy & Technology (official site). Archived from the original on مارس 8, 2009. Retrieved مارس 20, 2009.
- ^ ""National Network" of Fusion Centers Raises Specter of COINTELPRO". EPIC Spotlight on Surveillance. يونيو 2007. Retrieved مارس 14, 2009.
- ^ Myers, Lisa (ديسمبر 14, 2005). "Is the Pentagon spying on Americans?". NBC Nightly News. NBC News. Retrieved مارس 13, 2009.
- ^ "The Use of Informants in FBI Domestic Intelligence Investigations". Final Report: Book III, Supplementary Detailed Staff Reports on Intelligence Activities and the Rights of Americans. U.S. Senate Select Committee to Study Governmental Operations with Respect to Intelligence Activities. أبريل 23, 1976. pp. 225–270. Retrieved مارس 13, 2009.
- ^ "Secret Justice: Criminal Informants and America's Underground Legal System | Prison Legal News". www.prisonlegalnews.org. Retrieved أكتوبر 5, 2016.
- ^ Ross, Brian (يوليو 25, 2007). "FBI Proposes Building Network of U.S. Informants". Blotter. ABC News. Retrieved مارس 13, 2009.
- ^ "U.S. Reconnaissance Satellites: Domestic Targets". National Security Archive. Retrieved مارس 16, 2009.
- ^ Block, Robert (أغسطس 15, 2007). "U.S. to Expand Domestic Use Of Spy Satellites". The Wall Street Journal. Retrieved مارس 14, 2009.
- ^ Gorman, Siobhan (أكتوبر 1, 2008). "Satellite-Surveillance Program to Begin Despite Privacy Concerns". The Wall Street Journal. Retrieved مارس 16, 2009.
- ^ "Fact Sheet: National Applications Office". Department of Homeland Security (official website). أغسطس 15, 2007. Archived from the original on March 11, 2009. Retrieved March 16, 2009.
- ^ أ ب Warrick, Joby (أغسطس 16, 2007). "Domestic Use of Spy Satellites To Widen". The Washington Post. pp. A01. Retrieved مارس 17, 2009.
- ^ Shrader, Katherine (سبتمبر 26, 2004). "Spy imagery agency watching inside U.S." USA Today. Associated Press. Retrieved مارس 17, 2009.
- ^ Kappeler, Victor. "Forget the NSA: Police May be a Greater Threat to Privacy".
- ^ "Section 100i – IMS I-Catcher", The German Code Of Criminal Procedure, 2014, pp. 43–44
- ^ "Revealed: Saudis suspected of phone spying campaign in US". The Guardian. Retrieved مارس 29, 2020.
- ^ "Saudi Spies Tracked Phones Using Flaws the FCC Failed to Fix for Years". TechCrunch. Retrieved مارس 29, 2020.
- ^ أ ب "Two Stories Highlight the RFID Debate". RFID Journal. يوليو 19, 2005. Retrieved مارس 23, 2012.
- ^ أ ب Lewan, Todd (يوليو 21, 2007). "Microchips in humans spark privacy debate". USA Today. Associated Press. Retrieved مارس 17, 2009.
- ^ McCullagh, Declan (يناير 13, 2003). "RFID Tags: Big Brother in small packages". CNET News. Retrieved يوليو 24, 2012.
- ^ Gardener, W. David (يوليو 15, 2004). "RFID Chips Implanted In Mexican Law-Enforcement Workers". Information Week. Retrieved مارس 17, 2009.
- ^ Campbell, Monica (أغسطس 4, 2004). "Law enforcement in Mexico goes a bit bionic". Christian Science Monitor. Retrieved مارس 17, 2009.
- ^ Monahan, Torin; Fisher, Jill A. (2010). "Implanting inequality: Empirical evidence of social and ethical risks of implantable radio-frequency identification (RFID) devices". International Journal of Technology Assessment in Health Care. 26 (4). doi:10.1017/S0266462310001133. PMID 20923593.
- ^ Lyman, D., Micheal. Criminal Investigation: The Art and the Science. 6th ed. Pearson, 2010. p249
- ^ Crowder, Stan, and Turvery E. Brent. Ethical Justice: Applied Issues for Criminal Justice Students and Professionals. 1st ed. Academic Press, 2013. p150. Print.
- ^ Claburn, Thomas (مارس 4, 2009). "Court Asked To Disallow Warrantless GPS Tracking". Information Week. Retrieved مارس 18, 2009.
- ^ Hilden, Julie (أبريل 16, 2002). "What legal questions are the new chip implants for humans likely to raise?". CNN.com (FindLaw). Retrieved مارس 17, 2009.
- ^ Wolf, Paul. "COINTELPRO". (online collection of historical documents). Retrieved مارس 14, 2009.
- ^ Rooney, Julie Lynn (2017). "Going Postal: Analyzing the Abuse of Mail Covers Under the Fourth Amendment". Vanderbilt Law Review. 70[5]: 1627–1662.
- ^ "U.S. Army Intelligence Activities" (PDF). Archived from the original (PDF) on August 8, 2015. Retrieved 25 May 2015.
- ^ "Domestic CIA and FBI Mail Opening Programs" (PDF). Final Report: Book III, Supplementary Detailed Staff Reports on Intelligence Activities and the Rights of Americans. U.S. Senate Select Committee to Study Governmental Operations with Respect to Intelligence Activities. أبريل 23, 1976. pp. 559–678. Archived from the original (PDF) on مايو 5, 2011. Retrieved مارس 13, 2009.
- ^ Goldstein, Robert (2001). Political Repression in Modern America. University of Illinois Press. ISBN 978-0-252-06964-2.
- ^ أ ب Williams, Jamie Lee (2016). "Privacy in the Age of the Internet of Things". Human Rights. 41 (4): 14–22. ISSN 0046-8185. JSTOR 26423456.
- ^ Deviant Behaviour – Socially accepted observation of behaviour for security, Jeroen van Rest
- ^ Sprenger, Polly (يناير 26, 1999). "Sun on Privacy: 'Get Over It'". Wired Magazine. Retrieved مارس 20, 2009.
- ^ Baig, Edward; Marcia Stepanek; Neil Gross (أبريل 5, 1999). "Privacy". Business Week. Archived from the original on October 17, 2008. Retrieved March 20, 2009.
- ^ Solove, Daniel (2007). "'I've Got Nothing to Hide' and Other Misunderstandings of Privacy". San Diego Law Review. 44: 745. SSRN 998565.
- ^ أ ب ت "Is the U.S. Turning Into a Surveillance Society?". American Civil Liberties Union. Retrieved مارس 13, 2009.
- ^ أ ب "Bigger Monster, Weaker Chains: The Growth of an American Surveillance Society" (PDF). American Civil Liberties Union. يناير 15, 2003. Retrieved مارس 13, 2009.
- ^ "Privacy fears over online surveillance footage broadcasts in China". ديسمبر 13, 2017.
- ^ Marx, Gary T.; Muschert, Glenn W. (2007). "Personal Information, Borders, and the New Surveillance Studies" (PDF). Annual Review of Law and Social Science. 3: 375–395. doi:10.1146/annurev.lawsocsci.3.081806.112824. Archived from the original (PDF) on أغسطس 11, 2017.
- ^ أ ب Agre, Philip E. (2003), "Your Face is not a bar code: arguments against automatic face recognition in public places". Retrieved November 14, 2004.
- ^ Foucault, Michel (1979). Discipline and Punish. New York: Vintage Books. pp. 201–202.
- ^ أ ب ت ث ج Chayko, Mary (2017). Superconnected: the internet, digital media, and techno-social life. New York, NY: Sage Publications.
- ^ Nishiyama, Hidefumi (2017). "Surveillance as Race Struggle: On Browne's Dark Matters". Theory & Event. Johns Hopkins University Press. 20 (1): 280–285 – via Project MUSE.
- ^ Browne, Simone (أكتوبر 2, 2015). Dark Matters: On the Surveillance of Blackness. Duke University Press Books. p. 224. ISBN 978-0822359197.
- ^ Court of Appeal, Second District, Division 6, California. (يوليو 30, 2008). "People vs. Diaz". FindLaw. Retrieved فبراير 1, 2017.
{{cite web}}: CS1 maint: multiple names: authors list (link) CS1 maint: numeric names: authors list (link) - ^ California Fourth District Court of Appeal (يونيو 25, 2014). "Riley v. California". Oyez – IIT Chicago-Kent College of Law. Retrieved فبراير 1, 2013.
- ^ "The Secrets of Countersurveillance". Security Weekly. يونيو 6, 2007.
- ^ Birch, Dave (يوليو 14, 2005). "The age of sousveillance". The Guardian. London. Retrieved أغسطس 6, 2007.
- ^ أ ب ت Eggers, David (2013). The Circle. New York: Alfred A. Knopf, McSweeney's Books. pp. 288, 290–291, 486. ISBN 978-0-385-35139-3.
Further reading
| مراجع مكتبية عن مراقبة |
- Allmer, Thomas. (2012). Towards a Critical Theory of Surveillance in Informational Capitalism. Frankfurt am Main: Peter Lang. ISBN 978-3-631-63220-8
- Andrejevic, Mark. 2007. iSpy: Surveillance and Power in the Interactive Era. Lawrence, KS: University Press of Kansas. ISBN 0700616861
- Ball, Kirstie, Kevin D. Haggerty, and David Lyon, eds. (2012). Routledge Handbook of Surveillance Studies. New York: Routledge. ISBN 1138026026
- Brayne, Sarah. (2020). Predict and Surveil: Data, Discretion, and the Future of Policing. New York: Oxford University Press. ISBN 0190684097
- Browne, Simone. (2015). Dark Matters: On the Surveillance of Blackness. Durham: Duke University Press. ISBN 978-0822359197
- Coleman, Roy, and Michael McCahill. 2011. Surveillance & Crime. Thousand Oaks, Calif.: Sage. ISBN 1847873537
- Feldman, Jay. (2011). Manufacturing Hysteria: A History of Scapegoating, Surveillance, and Secrecy in Modern America. New York, NY: Pantheon Books. ISBN 0-375-42534-9
- Fuchs, Christian, Kees Boersma, Anders Albrechtslund, and Marisol Sandoval, eds. (2012). "Internet and Surveillance: The Challenges of Web 2.0 and Social Media". New York: Routledge. ISBN 978-0-415-89160-8
- Garfinkel, Simson, Database Nation; The Death of Privacy in the 21st Century. O'Reilly & Associates, Inc. ISBN 0-596-00105-3
- Gilliom, John. (2001). Overseers of the Poor: Surveillance, Resistance, and the Limits of Privacy, University Of Chicago Press, ISBN 978-0-226-29361-5
- Haque, Akhlaque. (2015). Surveillance, Transparency and Democracy: Public Administration in the Information Age. University of Alabama Press, Tuscaloosa, AL. ISBN 978-0-8173-1877-2
- Harris, Shane. (2011). The Watchers: The Rise of America's Surveillance State. London, UK: Penguin Books Ltd. ISBN 0-14-311890-0
- Hier, Sean P., & Greenberg, Joshua (Eds.). (2009). Surveillance: Power, Problems, and Politics. Vancouver, CA: UBC Press. ISBN 0-7748-1611-2
- Jensen, Derrick and Draffan, George (2004) Welcome to the Machine: Science, Surveillance, and the Culture of Control Chelsea Green Publishing Company. ISBN 978-1-931498-52-4
- Lewis, Randolph. (2017). Under Surveillance: Being Watched in Modern America. Austin: University of Texas Press. ISBN 1477312439
- Lyon, David (2001). Surveillance Society: Monitoring in Everyday Life. Philadelphia: Open University Press. ISBN 978-0-335-20546-2
- Lyon, David (Ed.). (2006). Theorizing Surveillance: The Panopticon and Beyond. Cullompton, UK: Willan Publishing. ISBN 978-1-84392-191-2
- Lyon, David (2007) Surveillance Studies: An Overview. Cambridge: Polity Press. ISBN 978-0-7456-3591-0
- Matteralt, Armand. (2010). The Globalization of Surveillance. Cambridge, UK: Polity Press. ISBN 0-7456-4511-9
- Monahan, Torin, ed. (2006). Surveillance and Security: Technological Politics and Power in Everyday Life. New York: Routledge. ISBN 9780415953931
- Monahan, Torin. (2010). Surveillance in the Time of Insecurity. New Brunswick: Rutgers University Press. ISBN 0813547652
- Monahan, Torin, and David Murakami Wood, eds. (2018). Surveillance Studies: A Reader. New York: Oxford University Press. ISBN 978-0-190-29782-4
- Parenti, Christian The Soft Cage: Surveillance in America From Slavery to the War on Terror, Basic Books, ISBN 978-0-465-05485-5
- Petersen, J.K. (2012) Handbook of Surveillance Technologies, Third Edition, Taylor & Francis: CRC Press, 1020 pp., ISBN 978-1-439873-15-1
- Staples, William G. (2000). Everyday Surveillance: Vigilance and Visibility in Post-Modern Life. Lanham, MD: Rowman & Littlefield Publishers. ISBN 0-7425-0077-2
General information
- "Special Issue on Surveillance Capitalism – nine articles analyzing financial, social, political, legal, historical, security and other aspects of US and international surveillance and spying programs and their relation to capitalism". Monthly Review. 2014. (Volume 66, Number 3, July–August)
- ACLU, "The Surveillance-Industrial Complex: How the American Government Is Conscripting Businesses and Individuals in the Construction of a Surveillance Society"
- Balkin, Jack M. (2008). "The Constitution in the National Surveillance State", Yale Law School
- Bibo, Didier and Delmas-Marty, "The State and Surveillance: Fear and Control"
- EFF Privacy Resources
- EPIC Privacy Resources
- ICO. (September 2006). "A Report on the Surveillance Society for the Information Commissioner by the Surveillance Studies Network".
- Privacy Information Center
- "The NSA Files (Dozens of articles about the U.S. National Security Agency and its spying and surveillance programs)". The Guardian. London. يونيو 8, 2013.
- Blunden, Bill (April 2015). Mass Surveillance is Driven by the Private Sector, in CounterPunch
Historical information
- COINTELPRO—FBI counterintelligence programs designed to neutralize political dissidents
- Reversing the Whispering Gallery of Dionysius – A Short History of Electronic Surveillance in the United States
Legal resources
External links
 Media related to مراقبة at Wikimedia Commons
Media related to مراقبة at Wikimedia Commons
- CS1 الإنجليزية البريطانية-language sources (en-gb)
- Articles with dead external links from August 2018
- CS1 maint: bot: original URL status unknown
- CS1 الإنجليزية الأمريكية-language sources (en-us)
- CS1 maint: numeric names: authors list
- Short description is different from Wikidata
- Articles with hatnote templates targeting a nonexistent page
- Missing redirects
- Use mdy dates from December 2012
- All Wikipedia articles needing clarification
- Wikipedia articles needing clarification from March 2012
- مقالات فيها عبارات متقادمة منذ 2012
- جميع المقالات التي فيها عبارات متقادمة
- جميع الصفحات التي تحتاج تنظيف
- مقالات بالمعرفة تحتاج توضيح from February 2016
- Surveillance
- Crime prevention
- Espionage techniques
- Law enforcement
- Law enforcement techniques
- National security
- Privacy
- Security