هجوم القوة العمياء
هجوم القوة العمياء (إنگليزية: brute-force attack)، في علم التعمية consists of an attacker submitting many passwords or passphrases with the hope of eventually guessing correctly. The attacker systematically checks all possible passwords and passphrases until the correct one is found. Alternatively, the attacker can attempt to guess the key which is typically created from the password using a key derivation function. This is known as an exhaustive key search.
A brute-force attack is a cryptanalytic attack that can, in theory, be used to attempt to decrypt any encrypted data (except for data encrypted in an information-theoretically secure manner).[1] Such an attack might be used when it is not possible to take advantage of other weaknesses in an encryption system (if any exist) that would make the task easier.
When password-guessing, this method is very fast when used to check all short passwords, but for longer passwords other methods such as the dictionary attack are used because a brute-force search takes too long. Longer passwords, passphrases and keys have more possible values, making them exponentially more difficult to crack than shorter ones.[2]
Brute-force attacks can be made less effective by obfuscating the data to be encoded making it more difficult for an attacker to recognize when the code has been cracked or by making the attacker do more work to test each guess. One of the measures of the strength of an encryption system is how long it would theoretically take an attacker to mount a successful brute-force attack against it.[3]
Brute-force attacks are an application of brute-force search, the general problem-solving technique of enumerating all candidates and checking each one.
المفهوم الأساسي
Brute-force attacks work by calculating every possible combination that could make up a password and testing it to see if it is the correct password. As the password's length increases, the amount of time, on average, to find the correct password increases exponentially.[4]
الحدود النظرية
The resources required for a brute-force attack grow exponentially with increasing key size, not linearly. Although U.S. export regulations historically restricted key lengths to 56-bit symmetric keys (e.g. Data Encryption Standard), these restrictions are no longer in place, so modern symmetric algorithms typically use computationally stronger 128- to 256-bit keys.
There is a physical argument that a 128-bit symmetric key is computationally secure against brute-force attack. The so-called Landauer limit implied by the laws of physics sets a lower limit on the energy required to perform a computation of kT • ln 2 per bit erased in a computation, where T is the temperature of the computing device in kelvins, k is the Boltzmann constant, and the natural logarithm of 2 is about 0.693. No irreversible computing device can use less energy than this, even in principle.[5] Thus, in order to simply flip through the possible values for a 128-bit symmetric key (ignoring doing the actual computing to check it) would, theoretically, require 2128 − 1 bit flips on a conventional processor. If it is assumed that the calculation occurs near room temperature (≈300 K), the Von Neumann-Landauer Limit can be applied to estimate the energy required as ≈1018 joules, which is equivalent to consuming 30 gigawatts of power for one year. This is equal to 30×109 W×365×24×3600 s = 9.46×1017 J or 262.7 TWh (about 0.1% of the yearly world energy production). The full actual computation – checking each key to see if a solution has been found – would consume many times this amount. Furthermore, this is simply the energy requirement for cycling through the key space; the actual time it takes to flip each bit is not considered, which is certainly greater than 0 (see Bremermann's limit).
However, this argument assumes that the register values are changed using conventional set and clear operations which inevitably generate entropy. It has been shown that computational hardware can be designed not to encounter this theoretical obstruction (see reversible computing), though no such computers are known to have been constructed.[بحاجة لمصدر]

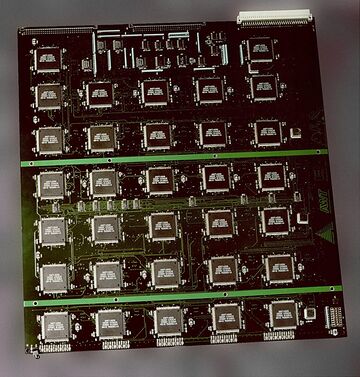
As commercial successors of governmental ASIC solutions have become available, also known as custom hardware attacks, two emerging technologies have proven their capability in the brute-force attack of certain ciphers. One is modern graphics processing unit (GPU) technology,[6][صفحة مطلوبة] the other is the field-programmable gate array (FPGA) technology. GPUs benefit from their wide availability and price-performance benefit, FPGAs from their energy efficiency per cryptographic operation. Both technologies try to transport the benefits of parallel processing to brute-force attacks. In case of GPUs some hundreds, in the case of FPGA some thousand processing units making them much better suited to cracking passwords than conventional processors. Various publications in the fields of cryptographic analysis have proved the energy efficiency of today's FPGA technology, for example, the COPACOBANA FPGA Cluster computer consumes the same energy as a single PC (600 W), but performs like 2,500 PCs for certain algorithms. A number of firms provide hardware-based FPGA cryptographic analysis solutions from a single FPGA PCI Express card up to dedicated FPGA computers.[بحاجة لمصدر] WPA and WPA2 encryption have successfully been brute-force attacked by reducing the workload by a factor of 50 in comparison to conventional CPUs[7][8] and some hundred in case of FPGAs.
Advanced Encryption Standard (AES) permits the use of 256-bit keys. Breaking a symmetric 256-bit key by brute force requires 2128 times more computational power than a 128-bit key. One of the fastest supercomputers in 2019 has a speed of 100 petaFLOPS which could theoretically check 100 million million (1014) AES keys per second (assuming 1000 operations per check), but would still require 3.67×1055 years to exhaust the 256-bit key space.[9]
An underlying assumption of a brute-force attack is that the complete key space was used to generate keys, something that relies on an effective random number generator, and that there are no defects in the algorithm or its implementation. For example, a number of systems that were originally thought to be impossible to crack by brute force have nevertheless been cracked because the key space to search through was found to be much smaller than originally thought, because of a lack of entropy in their pseudorandom number generators. These include Netscape's implementation of SSL (famously cracked by Ian Goldberg and David Wagner in 1995) and a Debian/Ubuntu edition of OpenSSL discovered in 2008 to be flawed.[10][11] A similar lack of implemented entropy led to the breaking of Enigma's code.[12][13]
إعادة تدوير بيانات الاعتماد
Credential recycling refers to the hacking practice of re-using username and password combinations gathered in previous brute-force attacks. A special form of credential recycling is pass the hash, where unsalted hashed credentials are stolen and re-used without first being brute forced.
رموز غير قابلة للكسر
Certain types of encryption, by their mathematical properties, cannot be defeated by brute force. An example of this is one-time pad cryptography, where every cleartext bit has a corresponding key from a truly random sequence of key bits. A 140 character one-time-pad-encoded string subjected to a brute-force attack would eventually reveal every 140 character string possible, including the correct answer – but of all the answers given, there would be no way of knowing which was the correct one. Defeating such a system, as was done by the Venona project, generally relies not on pure cryptography, but upon mistakes in its implementation: the key pads not being truly random, intercepted keypads, operators making mistakes – or other errors.[14]
التدابير المضادة
In case of an offline attack where the attacker has access to the encrypted material, one can try key combinations without the risk of discovery or interference. However database and directory administrators can take countermeasures against online attacks, for example by limiting the number of attempts that a password can be tried, by introducing time delays between successive attempts, increasing the answer's complexity (e.g. requiring a CAPTCHA answer or verification code sent via cellphone), and/or locking accounts out after unsuccessful login attempts.[15][صفحة مطلوبة] Website administrators may prevent a particular IP address from trying more than a predetermined number of password attempts against any account on the site.[16]
عكس الهجوم المضاد
In a reverse brute-force attack, a single (usually common) password is tested against multiple usernames or encrypted files.[17] The process may be repeated for a select few passwords. In such a strategy, the attacker is not targeting a specific user.
انظر أيضاً
- Bitcoin mining
- Cryptographic key length
- Distributed.net
- Key derivation function
- MD5CRK
- Metasploit Express
- هجوم القناة الجانبية
- TWINKLE and TWIRL
- Unicity distance
- RSA Factoring Challenge
- پروتوكول النقل الآمن
الهوامش
- ^ Paar, Pelzl & Preneel 2010, p. 7.
- ^ Urbina, Ian (2014). "The Secret Life of Passwords. The New Times". The New York Times.
{{cite news}}: CS1 maint: url-status (link) - ^ Schrittwieser, Sebastian; Katzenbeisser, Stefan (2011), Code Obfuscation against Static and Dynamic Reverse Engineering, Lecture Notes in Computer Science, 6958, Berlin, Heidelberg: Springer Berlin Heidelberg, pp. 270–284, doi:, ISBN 978-3-642-24177-2, http://dx.doi.org/10.1007/978-3-642-24178-9_19, retrieved on 2021-09-05
- ^ "Brute Force Attack: Definition and Examples". www.kaspersky.com (in الإنجليزية). 2020-10-20. Retrieved 2020-11-08.
- ^ Landauer 1961, p. 183-191.
- ^ Graham 2011.
- ^ Kingsley-Hughes 2008.
- ^ Kamerling 2007.
- ^ "November 2019 | TOP500 Supercomputer Sites". www.top500.org. Archived from the original on November 19, 2019. Retrieved 2020-05-15.
- ^ Viega, Messier & Chandra 2002, p. 18.
- ^ CERT-2008.
- ^ Ellis.
- ^ NSA-2009.
- ^ Reynard 1997, p. 86.
- ^ Burnett & Foster 2004.
- ^ Ristic 2010, p. 136.
- ^ "InfoSecPro.com - Computer, network, application and physical security consultants". www.infosecpro.com. Archived from the original on 4 April 2017. Retrieved 8 May 2018.
المصادر
- (June 10–12, 1996) "On Applying Molecular Computation To The Data Encryption Standard"., Princeton University.
- Cracking DES – Secrets of Encryption Research, Wiretap Politics & Chip Design. Electronic Frontier Foundation. 1998. ISBN 1-56592-520-3.
- Burnett, Mark; Foster, James C. (2004). Hacking the Code: ASP.NET Web Application Security. Syngress. ISBN 1-932266-65-8.
- Diffie, W.; Hellman, M.E. (1977). "Exhaustive Cryptanalysis of the NBS Data Encryption Standard". Computer. 10: 74–84. doi:10.1109/c-m.1977.217750. S2CID 2412454.
- Graham, Robert David (22 June 2011). "Password cracking, mining, and GPUs". erratasec.com. Retrieved 17 August 2011.
- Ellis, Claire (March 2005). "Exploring the Enigma". Plus Magazine.
- Kamerling, Erik (2007-11-12). "Elcomsoft Debuts Graphics Processing Unit (GPU) Password Recovery Advancement". Symantec.
- Kingsley-Hughes, Adrian (2008-10-12). "ElcomSoft uses NVIDIA GPUs to Speed up WPA/WPA2 Brute-force Attack". ZDNet.
- Landauer, L (1961). "Irreversibility and Heat Generation in the Computing Process". IBM Journal of Research and Development. 5 (3): 183–191. doi:10.1147/rd.53.0183.
- Paar, Christof; Pelzl, Jan; Preneel, Bart (2010). Understanding Cryptography: A Textbook for Students and Practitioners. Springer. ISBN 978-3-642-04100-6.
- Reynard, Robert (1997). Secret Code Breaker II: A Cryptanalyst's Handbook. Jacksonville, FL: Smith & Daniel Marketing. ISBN 1-889668-06-0. Retrieved 2008-09-21.
- Ristic, Ivan (2010). Modsecurity Handbook. Feisty Duck. ISBN 978-1-907117-02-2.
- Viega, John; Messier, Matt; Chandra, Pravir (2002). Network Security with OpenSSL. O'Reilly. ISBN 0-596-00270-X. Retrieved 2008-11-25.
- Wiener, Michael J. (1996). "Efficient DES Key Search". Practical Cryptography for Data Internetworks. W. Stallings, editor, IEEE Computer Society Press.
- "Technical Cyber Security Alert TA08-137A: Debian/Ubuntu OpenSSL Random Number Generator Vulnerability". United States Computer Emergency Readiness Team (CERT). 2008-05-16. Retrieved 2008-08-10.
- "NSA's How Mathematicians Helped Win WWII". National Security Agency. 15 Jan 2009.
وصلات خارجية
- RSA-sponsored DES-III cracking contest
- Demonstration of a brute-force device designed to guess the passcode of locked iPhones running iOS 10.3.3
- How We Cracked the Code Book Ciphers – Essay by the winning team of the challenge in The Code Book
- CS1 maint: url-status
- Short description is different from Wikidata
- Articles containing إنگليزية-language text
- Pages using Lang-xx templates
- Articles with unsourced statements from September 2010
- مقالات بالمعرفة بحاجة لذكر رقم الصفحة بالمصدر from March 2012
- Articles with unsourced statements from November 2010
- هجمات تعموية